Email encryption and email archiving: How can the two be combined? - TechGenix
Email encryption and email archiving: How can the two be combined? - TechGenix |
- Email encryption and email archiving: How can the two be combined? - TechGenix
- How to Send Encrypted Email on 3 Major Email Platforms - Hashed Out by The SSL Store™
- Barr says the US needs encryption backdoors to prevent "going dark." Um, what? - Stock News Brief
| Email encryption and email archiving: How can the two be combined? - TechGenix Posted: 25 Sep 2019 05:32 AM PDT Do you already know how email encryption works and which different encryption methods are available? And how to combine email encryption with an email archiving solution? In fact, is it actually possible to archive encrypted emails? If you have no answer to these questions yet, this blog post will help you understand the basics of email encryption and email archiving and show you how to archive encrypted emails. But let's start at the beginning. Why do we use email encryption in the first place? Emails travel from one server to the next on their way from sender to recipient. If they are not encrypted prior to sending, they are vulnerable to attack by third parties both en route and on the servers themselves. Crooks could intercept or even tamper with these emails, which is why it is advisable to encrypt sensitive data. The financial or reputational loss resulting from an attack on personal or corporate data can be considerable; nor should the repercussions of violations of the GDPR be underestimated. According to a Virtru study, only significantly less than 50 percent of emails are client-side encrypted, many people regard encryption as simply too complex. We'll look at what is meant by too complex later on in this post. Which parts of an email are actually encrypted? Only the actual body of the email is encrypted: It is not possible to encrypt information such as the sender, recipient, destination, date of delivery, IP address, and subject line. Yet because even this data will often harbor internal and sensitive information, it is up to the respective company to decide whether email encryption actually makes sense and adds value. Apropos: Transport Encryption In order to keep an email's subject line and its content as secret as possible, and to provide a certain measure of protection against the unauthorized reading of unencrypted emails during transmission, SSL/TLS encryption at transport level should ideally always be used. In fact, this approach is already much more widely used than email encryption itself. Another reason for the more widespread use of transport encryption is the EU's GDPR that entered into force at the end of May 2018. Professional software solutions, such as MailStore Server for email archiving, attach great importance to transport encryption. After this brief introduction to the subject of email encryption, we want to explain why an email archiving solution really should form part of your overall data governance strategy. Why do we use email archiving in the first place? Every day, a wealth of information, including invoices, contracts, and other business-critical content is sent around the globe in the form of emails. With an email archiving solution in place emails can be stored on a long-term basis and their contents remain unchanged. Email archiving primarily serves the purposes of making data retrievable and available for a longer period of time. In addition, it serves the purpose of preventing data loss and documentation. This is why a professional email archiving solution should be a significant component of your data governance strategy. But how do you archive something that's encrypted? As a general principle, emails are archived in the form in which they enter the archive, so encrypted emails remain encrypted even during archiving and cannot be read by users, e.g. when conducting an archive search. In order to combine email encryption with an email archiving solution in a purposeful way, it is important to compare the different encryption methods and consider the disadvantages in each case, which we will examine again at a later stage. Client-based or server-based encryption? Encryption and decryption can take place either on the clients – known as conventional client-based (or end-to-end) encryption – or on the email server or an email gateway (generally a firewall), in which case it is server-based:
Apropos: Asymmetric Encryption The most common email encryption processes, S/MIME and PGP, always use asymmetric encryption. This type of encryption was developed in the early 1980s and comprises pairs of keys. The public key used to encrypt messages may be disseminated widely, while the private key used exclusively to decrypt the information is known only to the recipient and is generally also password protected. Incidentally, the same keys are used for digital signatures. In this case, the private key is used to sign the email and the public key to verify the signature. Disadvantages of the two encryption methods In order to settle the issue of which type of encryption is better suited to email archiving, we need to look at the disadvantages of the two processes in more detail, as both client-based and server-based encryption are feasible: Disadvantages of client-based encryption:
Disadvantages of server-based encryption:
Our conclusion Despite several disadvantages, email encryption is useful and necessary for certain types of company. Client-based encryption can entail a number of complications – for example when it comes to email archiving, however. We, therefore, recommend the use of server-based email encryption. To sum up, server-based encryption offers the following key advantages:
Sponsored by MailStore Software Images: Shutterstock Post Views: 3  Read Next |
| How to Send Encrypted Email on 3 Major Email Platforms - Hashed Out by The SSL Store™ Posted: 03 Jun 2019 12:00 AM PDT Your step-by-step guide to sending encrypted email via Gmail, Outlook, and Mac MailNews of cyber attacks and data breaches is continually making headlines. Sometimes, these breaches are the result of phishing attacks and poor employee email practices — other times, they occur because sensitive information is left unprotected, is sent via unsecure channels, or businesses fail to meet regulatory cyber security requirements. This is why upping your email security protections is vital to the safety and success of your company and customers. Choosing the best way to accomplish this goal can be challenging. Of course, you can (and should) provide cyber security awareness training to your employees to teach them how to follow email security best practices (using strong passwords, not sending sensitive business or customer data over unsecure channels, etc.). But that's only one piece of the puzzle — employee training shouldn't be your only solution. Beyond this approach, the next best way to help protect your sensitive data is to use email encryption and identity verification methods such as digital signing certificates. After all, every unencrypted email you send with sensitive information (personal information, financial data, product specs, etc.) is vulnerable and, therefore, leaves your business and customers at risk. Not sure how to secure email with digital signing certificates so your messages can't be read by unintended third parties? No worries. We'll break down the process for how email signing and encryption certificates work and how you and your organization can send encrypted email communications using them on different email platforms. Let's hash it out. How to Secure Email Using S/MIME Email Encryption Certificates Depending on your country and industry — such as finance, retail, eCommerce, or healthcare — you may have stringent requirements to meet concerning data protection. In many cases, you'll need to use encrypted emails to meet these requirements. (In the case of HIPAA, though, they're "administrative safeguards.") Staying compliant not only helps you protect your business, but it also helps you avoid costly fines and lawsuits stemming from noncompliance. Companies use different methods for encrypting their emails — transport layer security (TLS), Pretty Good Privacy (PGP), third-party email clients such as ProtonMail, third-party and native web browser and email client plugins and extensions, etc. Each of these methods have pros and cons associated with them:
Another popular email encryption method is the use of S/MIME certificates (S/MIME stands for secure/multipurpose internet mail extensions). These certificates:
S/MIME certificates are used to encrypt emails before they are sent to a mail server or across the internet where hackers and malicious users can read them. Is S/MIME perfect? No. The downside of S/MIME is that to use it, an S/MIME certificate first needs to be installed to your individual computer or device's email client. In the past, this was done manually. However, using a zero-touch S/MIME solution to automate the issuance and deployment of S/MIME certificates makes the process of managing multiple (or hundreds) of these digital certificates for your business simple. This solution also helps you to ensure that your certificates are renewed before their expiry date. How S/MIME Works We've previously discussed the what S/MIME is and how it works at length, so we won't go into depth about that here. But here's a quick recap to refresh your memory: SSL or TLS provides server to server encryption, which protects your email while it's in transit. S/MIME, on the other hand, uses asymmetric encryption to protect your email data both in transit and when it's at rest. Basically, you use a public key to encrypt the email data and your recipient uses a matching private key to decrypt it. Note: For S/MIME encryption to work, both you (the sender) and your intended recipient need to have encryption enabled, and you need to have the recipient's public key to encrypt your messages so only they can decrypt them. A simple way to ensure that you and your recipient have the matching public/private keys is to send each other a signed certificate email prior to sending them an encrypted email. This way you'll each have the other's public key for encrypting emails. Essentially, the difference between using SSL email encryption and sending an encrypted email is the difference between securing your channel (data in transit) and protecting the message itself (data at rest data protection). Let's consider the following example:
Using email encryption ensures that the message and attachments of your email are protected before they are ever sent to a mail server and will remain secure/encrypted until your recipient with the private key accesses it. So, rather than only protecting the communication channel, you're protecting the message itself. Step by Step: How to Send Encrypted Email on Three Mail ClientsRegardless of which email client or platform you use, the first step to using S/MIME entails getting an email encryption certificate, which you can do by purchasing one directly from a certificate authority (CA) or a reputable reseller. The next step is installing the certificate on your email client/platform. Seeing as how S/MIME certificates is kind of what we do — along with providing other digital security solutions such as SSL certificates, PKI management platforms, etc. — we've already written articles on how to install these certificates on Outlook for Mac and Windows systems. For explicit directions on how to install these certificates, check out these Apple– and Windows-focused articles. Assuming that you already have these certificates installed, we'll move on to our step-by-step directions for how to send encrypted email in the following three mail clients: Google Suite, Outlook 2016, and Mac Mail. How to Send an Encrypted Email in Gmail Although Google promised end-to-end email encryption for users on their Gmail platform nearly five years ago, the internet giant has yet to follow through on their word. For a period, G Suite was selling and supporting Zix's G Suite Mail Encryption (GAME) as its own form of email encryption. However, since April 30, 2018, Google no longer sells or supports the service. The good news? Businesses using G Suite can use S/MIME. The catch? It's hosted S/MIME, which means that Google hosts clients' S/MIME certificates on its servers. Google's Gmail email services offer Basic, Business, and Enterprise. The company's site shows that all three use TLS server-to-server encryption. However, only the Enterprise level users (G Suite Enterprise and G Suite Enterprise for Education users) can take advantage of hosted S/MIME encryption. You'll need to enable S/MIME in Google Admin console for G Suite and upload your certificate to Google's server. Once this is done, you can encrypt and digitally sign your outgoing emails in Google Suite (Enterprise or Education) by doing the following:
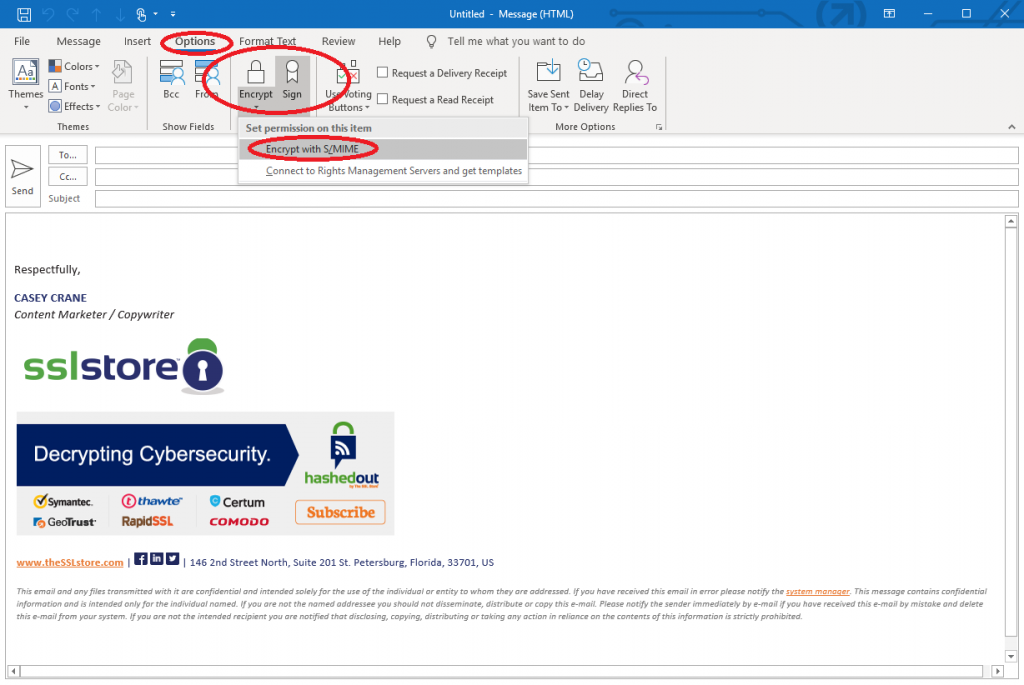
How to Send an Encrypted Email in Outlook 2016Encrypting an email — or all outgoing messages — is a pretty straightforward process in Outlook. Once you've installed your certificate, there's really nothing to it. To encrypt an outgoing email in Outlook 2016:
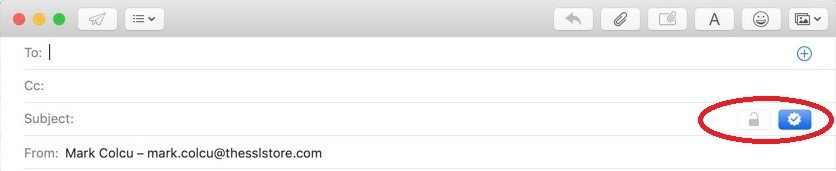
 … And that's it. It's really that simple. Mac Mail Encryption: How to Send Encrypted Email in Mac MailDon't worry, Apple users — we haven't forgotten about you. The great news for Apple users who wish to increase their email security is that Apple Mail supports S/MIME right out of the box. This means that when you purchase and install an S/MIME certificate, you don't have to jump through a bunch of hoops to use it. They really make it easy. Once you upload the certificate to your computer's key store, Mac Mail sets up the cert automatically for digital signing and the option for encryption. There is no required configuration outside of the keychain access utility. You can simply click to activate/deactivate signing and encryption. Again, the user would need to have the recipient's public key to encrypt to a (or many) recipients. What this means is that to send an encrypted and digitally signed email using Apple Mail:
 It doesn't get much easier than that. Final ThoughtsEmail signing and encryption are a must for businesses in a digital world. Every day, major companies are making headlines by falling prey to phishing scams — and small businesses aren't safe from these attacks, either. We can honestly say that we don't want to see your business as one of the next related headlines. Are you not seeing these options for your email client? That may be because you need to purchase and install an S/MIME certificate. Without it, you won't be able to gain access to the email signing and encryption capabilities we discussed in this article. Whether you're a small or midsize business (SMB) or a large corporation, our team can help you find the right certificate to meet your needs. Hit us up with any questions or to learn more. Have insights or questions about this topic? Feel free to share them below. |
| Barr says the US needs encryption backdoors to prevent "going dark." Um, what? - Stock News Brief Posted: 23 Sep 2019 04:00 PM PDT / US Attorney General William Barr speaks at the International Conference on Cyber Security at Fordham University School of Law on July 23, 2019 in New York City. In his remarks, Barr stated that increased encryption of data on phones and encrypted messaging apps puts American security at risk. Barr encouraged technology companies to provide law enforcement with access to encrypted data during certain criminal investigations.Drew Angerer/Getty Images Share this storyOn July 23, in a keynote address at the , US Attorney General William Barr took up a banner that the Justice Department and Federal Bureau of Investigation have : the call for what former FBI director James Comey had referred to as a "golden key." Citing the threat posed by violent criminals using encryption to hide their activities from law enforcement, Barr said that information security "should not come at the expense of making us more vulnerable in the real world." He claimed that this is what is happening today. "Service providers, device manufacturers, and application developers are developing and deploying encryption that can only be decrypted by the end user or customer, and they are refusing to provide technology that allows for lawful access by law enforcement agencies in appropriate circumstances," Barr proclaimed. And this, he said, was making it increasingly difficult for law enforcement to surveil criminal activity. This blindspot what also allowing criminals to make their information and communications "warrant proof… extinguishing the ability of law enforcement to obtain evidence essential to detecting and investigating crimes," and allowing "criminals to operate with impunity, hiding their activities under an impenetrable cloak of secrecy." Further ReadingIn other words, the lawful surveillance capabilities of the government are "going dark," according to AG Barr. "The net effect is to reduce the overall security of society," he continued. "I am here today to tell you that, as we use encryption to improve cybersecurity, we must ensure that we retain society's ability to gain lawful access to data and communications when needed to respond to criminal activity." AG Barr closed by saying that US citizens should accept encryption backdoors because backdoors are essential to our security. In response, Gen. Michael Hayden, former director of the National Security Agency, said, "Not really."
Regardless of the accuracy of Barr's claims, encryption is certainly far more prevalent than it was even five years ago—back when Edward Snowden gave the world a look at the workings of US intelligence agencies' digital surveillance capabilities. For better or worse, Snowden's data dump continues to shake up not just the world's view of communication privacy—it upended the world's view of information security in general. . But his revelations had wide-ranging effects on the tech industry and on the development of Internet and security standards. While Snowden opened up a dialogue about intelligence policy, "some of the most significant reforms were technical, not legal." That's according to Ben Wizner of the American Civil Liberties Union, who has acted as Snowden's attorney. "The proliferation of encryption was rapidly accelerated," he says. "And the Internet is more secure today than it was in 2013. Technology companies realized that they had been operating under the wrong threat model." After Snowden, Internet and technology firms could no longer ignore the threat posed by state-funded actors to their customers, said Mark Rumold, senior staff attorney at the Electronic Frontier Foundation (EFF). He went on:
Just how much those steps have hindered legal surveillance and investigation—attempts by law enforcement and intelligence agencies operating under the authority of a court-approved warrant—is in dispute. As information security professional Robert Graham pointed out in , there is no evidence of a surge in crime corresponding to the use of encryption. Such claims, he says, are "based on emotional anecdotes rather than statistics." Even allegedly hard data presented by the government . In December 2017, FBI Director Christopher Wray claimed in Congressional testimony that, in the 2017 fiscal year, the bureau "was unable to access the content of approximately 7,800 mobile devices" using available tools. Wray made this proclamation a year after the government's in the wake of the tragedy in San Bernardino, California. But that figure was vastly larger than the 880 devices the FBI had cited a year before, and a Washington Post investigation found that the number of inaccessible devices in 2017 was actually about 1,200 according to an FBI internal estimate. So, is surveillance really "going dark"? Or is this, as Graham suggested, "a Golden Age of Surveillance" where even more privacy is required? Joseph Lorenzo Hall, Chief Technologist at the Center for Democracy and Technology (CDT), leans toward the latter. "The FBI says they're 'going dark'," Hall told Ars. "Well yeah, because they've been staring at the sun." Fixing overexposureLike this prison in Cuba, the NSA has turned the Internet into a place where the watchmen can see all and exploit the shoddy privacy of Internet services prior to Snowden. Much of the Internet has become more secure over the past five years. The Snowden revelations may not have directly caused the rise of secure Web protocols, but they sure helped motivate protocol development. While the threat of a "global observer" on the Internet had been theorized before Snowden, his evidence of that sort of capability immediately triggered a response from the technical community. "The engineering community took the succession of Snowden revelations really seriously," Hall told Ars. Just 11 months after the first of the leaks, the Internet Engineering Task Force put out , "stating that pervasive monitoring is an attack," Hall noted. Further ReadingTo be fair, the Internet in 2014 had practically nowhere to go but up in terms of protecting privacy. Almost all of the fundamental building blocks of the Internet were, at the time, "almost completely insecure" since their creation, Hall explained. That's "because we were experimenting with them. And now we're retroactively having to go back and put security back on." That shift in perception of the threat of mass surveillance was followed by significant improvements in securing Web traffic. That included much more security-focused operations at major Internet service providers. Two particular changes were accelerated by the Snowden revelations: adoption of secure HTTP (HTTPS) and TLS encryption by major Internet services, and the development of Transport Layer Security (TLS) 1.3. HTTPS has had the biggest effect so far, and the changes in TLS will further close the door on surveillance. In 2013, less than 30% of Web traffic was encrypted, and less than 10% of websites supported secure connections. By 2017, more than half of the Web supported HTTPS, and today over 70% of Web traffic is encrypted, based on data from and . As of April 2019, 91% of webpages visited by US users were secured. Internationally, about 85% of webpages visited were encrypted. Adoption of encryption for email traffic—both between client and server and from provider to provider—also grew dramatically as a direct result of the Snowden revelations. In early 2014, only about a quarter of the email traffic between Google and other providers was encrypted. Now, it's over 75%. The adoption of encryption has had major implications for both the intelligence community and law enforcement, at least in terms of "traditional" Internet traffic. Much of the metadata we examined in that was usable for surveillance by the NSA's XKeyscore system has become much less accessible. We re-staged the tests recently, using ourselves as the victim. Many of the identifiers and other content we were able to pick out of passive traffic collection in 2014 have been dramatically reduced. That isn't to say that they're gone—they're just concealed within encrypted HTTPS and TLS traffic now, at least for standard Web and email traffic. This practical consideration may be directly responsible for (searching the contents of traffic for communications that mentions specific keywords or identifiers for persons of interest). But there are still other ways to gather surveillance data from Internet traffic that won't be going dark anytime soon. Listing image by Markus Gann / EyeEm via Getty Images |
| You are subscribed to email updates from "encrypted email,secure phone line,what can be encrypted" - Google News. To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google, 1600 Amphitheatre Parkway, Mountain View, CA 94043, United States | |

Comments
Post a Comment