New Attack Lets Hackers Decrypt VoLTE Encryption to Spy on Phone Calls - Internet
New Attack Lets Hackers Decrypt VoLTE Encryption to Spy on Phone Calls - Internet |
- New Attack Lets Hackers Decrypt VoLTE Encryption to Spy on Phone Calls - Internet
- Why You Should Stop Using Facebook Messenger - Forbes
- The importance of security, data encryption for cloud - TechTarget
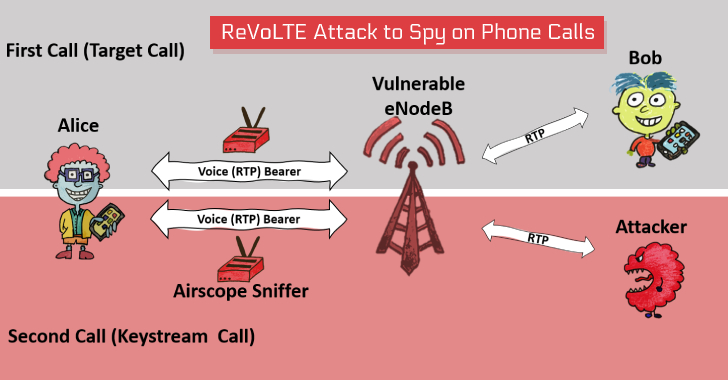
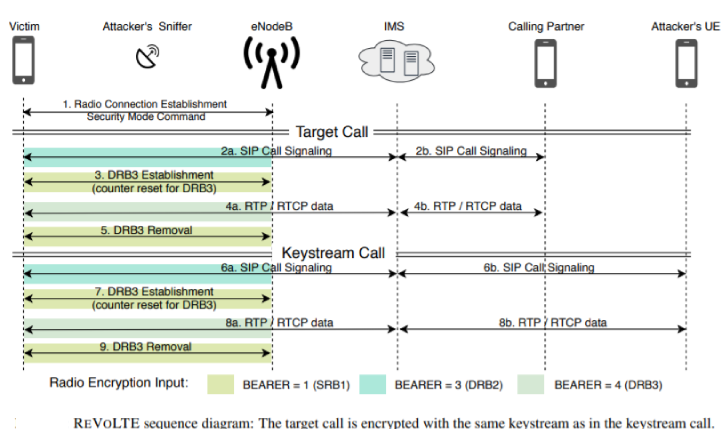
| New Attack Lets Hackers Decrypt VoLTE Encryption to Spy on Phone Calls - Internet Posted: 13 Aug 2020 06:09 AM PDT A team of academic researchers—who previously made the headlines earlier this year for uncovering severe security issues in the 4G LTE and 5G networks—today presented a new attack called 'ReVoLTE,' that could let remote attackers break the encryption used by VoLTE voice calls and spy on targeted phone calls. The attack doesn't exploit any flaw in the Voice over LTE (VoLTE) protocol; instead, it leverages weak implementation of the LTE mobile network by most telecommunication providers in practice, allowing an attacker to eavesdrop on the encrypted phone calls made by targeted victims. VoLTE or Voice over Long Term Evolution protocol is a standard high-speed wireless communication for mobile phones and data terminals, including Internet of things (IoT) devices and wearables, deploying 4G LTE radio access technology. The crux of the problem is that most mobile operators often use the same keystream for two subsequent calls within one radio connection to encrypt the voice data between the phone and the same base station, i.e., mobile phone tower. Thus, the new ReVoLTE attack exploits the reuse of the same keystream by vulnerable base stations, allowing attackers to decrypt the contents of VoLTE powered voice calls in the following scenario. However, reuse of a predictable keystream is not new and was first pointed out by Raza & Lu, but the ReVoLTE attack turns it into a practical attack. How Does the ReVoLTE Attack Work?To initiate this attack, the attacker must be connected to the same base station as the victim and place a downlink sniffer to monitor and record a 'targeted call' made by the victim to someone else that needs to be decrypted later, as part of the first phase of ReVoLTE attack. Once the victim hangs up the 'targeted call,' the attacker is required to call the victim, usually within 10 seconds immediately, which would force the vulnerable network into initiating a new call between victim and attacker on the same radio connection as used by previous targeted call.
Once connected, as part of the second phase, the attacker needs to engage the victim into a conversation and record it in plaintext, which would help the attacker later reverse compute the keystream used by the subsequent call. According to researchers, XOR-ing the keystreams with the corresponding encrypted frame of the targeted call captured in the first phase decrypts its content, allowing attackers to listen to what conversation its victim had in the previous phone call. "As this results in the same keystream, all RTP data is encrypted in the same way as the voice data of the target call. As soon as a sufficient amount of keystream data was generated, the adversary cancels the call," the paper reads. However, the length of the second call should be greater than or equal to the first call in order to decrypt each frame; otherwise, it can only decrypt a part of the conversation.
Detecting ReVoLTE Attack and DemonstrationTo demonstrate the practical feasibility of the ReVoLTE attack, the team of academics from Ruhr University Bochum implemented an end-to-end version of the attack within a commercial, vulnerable network and commercial phones. The team used the downlink analyzer Airscope by Software Radio System to sniff the encrypted traffic and three Android-based phones to obtain the known-plaintext at the attacker's phone. It then compared the two recorded conversations, determined the encryption key, and finally decrypted a portion of the previous call. You can see the demo video of the ReVoLTE attack, which, according to the researchers, could cost less than $7000 to attackers for setting up the attack and, eventually, decrypting downlink traffic. The team tested a number of randomly selected radio cells across Germany to determine the scope of the issue and found that it affects 12 out of 15 base stations in Germany, but researchers said the security gap also affects other countries. Researchers notified the affected German base station operators about the ReVoLTE attack through the GSMA Coordinated Vulnerability Disclosure Programme process in early December 2019, and the operators managed to deploy the patches by the time of publication. Since the issue also affects a large number of providers worldwide, researchers released an open source Android app, called 'Mobile Sentinel,' that you can use to detect whether their 4G network and base stations are vulnerable to the ReVoLTE attack or not. Researchers—David Rupprecht, Katharina Kohls and Thorsten Holz of RUB University Bochum and Christina Pöpper of NYU Abu Dhabi—have also released a dedicated website and research paper PDF, titled "Call Me Maybe: Eavesdropping Encrypted LTE Calls With REVOLTE," detailing the ReVoLTE attack, where you can find more details. |
| Why You Should Stop Using Facebook Messenger - Forbes Posted: 25 Jul 2020 12:00 AM PDT  SOPA Images/LightRocket via Getty Images If you're one of the hundreds of millions using Facebook Messenger, then now would be a good time to think about alternatives. While the platform heralded a major security update this week, with the addition of biometric device locks on iOS, the sad truth is that Messenger is seriously lacking on the security front. And this is a problem which is both getting worse and which Facebook cannot easily fix. In announcing its latest feature updates, Facebook told users that "privacy is at the heart of Messenger—where you can be yourself with the people who matter most to you." The company said that App Lock would "add another layer of security to your private messages to help prevent other people accessing them." Unfortunately, this update is akin to adding extra locks to the front door of a bank, while leaving the vault wide open. It's peripheral at best. There are now alternatives that offer most of the same functionality without the risks. It's time to switch. So, what's the problem. In a word—encryption. Don't take my word for it—Facebook itself warns users of the risks when messages are not end-to-end encrypted. This security measure, the company admits, would mitigate the compromise of server and networking infrastructure used by Messenger—Facebook's included." The company issued that warning in 2017, when introducing its "secret conversations." Recommended For You Secret conversations enable opt-in end-to-end encryption for specific person-to-person Messenger chats, not for groups and not by default. "A secret conversation in Messenger is end-to-end encrypted and intended just for you and the person you're talking to," Facebook says, implying that messages which are not "secret" risk being accessed by more than "just you and the person you're talking to." Facebook has created a serious problem for itself with Messenger. The company has become the world's leading advocate for end-to-end encryption, even CEO Mark Zuckerberg has personally lauded its benefits. But the company has also admitted that the technical complexities of adding this level of security to Messenger will take years. So—you're not as secure as you should be, but if you can just hang on a few years, we'll be sure to get that sorted for you. Really? Just look at WhatsApp's explanation for why it's needed: "Some of your most personal moments are shared with WhatsApp," it says, "which is why we built end-to-end encryption into our app. When end-to-end encrypted, your messages, photos, videos, voice messages, documents, and calls are secured from falling into the wrong hands." WhatsApp is of course owned by Facebook. Enough said. This issues aren't limited to Facebook Messenger, of course. SMS messaging is even worse. But that has become fairly well understood now. The straightforward advice is to stop using SMS if possible. Apple's iMessage and Google's rumoured encryption plans for RCS—an SMS replacement—both provide an end-to-end encryption update option for SMS, still the world's most pervasive mobile messaging platform. But Messenger has more than a billion users—and unlike SMS it presents as an updated and fully featured alternative to legacy messaging. "Users choosing to communicate via Messenger must understand the real threat to their information within such apps," warns ESET cybersecurity guru Jake Moore. "Although many may think the content in their messages isn't personal, the real issue is that any information on you is open to abuse in the wrong hands." If you have any doubts, take a look at Twitter's recent public shaming. No-one should be surprised at Twitter's admission that the recent hack of more than 100 users also tapped into private messages for 36 accounts. Twitter DMs are not end-to-end encrypted—just like Messenger, it's been stuck on the roadmap for years. Twitter is not a private messaging platform—its volume of DMs is a fraction of those sent over Messenger. But take it as a warning. "After the recent complications with Twitter," Moore says, "it highlights once again the importance of end-to-end encrypted messages and privacy focused messaging platforms." The Twitter attack specifically framed the vulnerability when a platform holds the keys to decrypt your private conversations. They may use those keys if asked by law enforcement, but there is also a risk that rogue or tricked employees may do the same. Facebook told me that "our servers are only in a handful of countries that have strong rule of law. We also have strong data protections and safeguards in place that secures data at rest and restricts employee access to message content." But, as uber-secure ProtonMail points out, "the best way to protect data is to not have access to it at all. The benefit of using end-to-end encrypted services is that data can be kept safe even in the event of the inevitable data breach because the service provider itself does not have the ability to decrypt user data. In effect, it is impossible for hackers to steal something that the service itself does not possess." There's a warning in there for even the more secure messaging apps. Apple and Google messaging back-ups are not end-to-end encrypted, they basically store a copy of your phone's decrypted data. And when you use the current WhatsApp cloud back-up feature, you run that same risk—this, though, is now being fixed. Moore advocates Signal—the platform of choice for cyber experts, with its security-first approach and no form of messaging back-up—as does infosec writer John Opdenakker. "People should consider everything they say in Twitter DMs or via Facebook Messenger can become public sooner or later," Opdenakker tells me. "If you want private messaging use apps like Signal that offer end-to-end encryption." Moore also recommends Telegram—a slightly more complex option. Telegram does not end-to-end encrypt by default. The issue, it explains, is that in doing so it becomes impossible for users to easily access messages on different devices from central repositories or to restore their history when a device is lost and replaced. Telegram does adopt a security-first approach, though, distributing the encryption keys it holds across different jurisdictions to frustrate any internal attempts—whether malicious or at the request of security agencies—to access content. Security professionals will always recommend the likes of Signal, where feature updates will only be introduced when they do not compromise security. In reality, though, you don't need to look further than WhatsApp. The world's most popular platform is end-to-end encrypted by default—it does this for individual chats and groups as well as for voice and video calls, again even when those extend to groups. WhatsApp has had its security wobbles over the years, but its end-to-end encryption has not been compromised. Hackers target devices, not the platform, because each end of an encrypted chat is a decrypted vulnerability. Even Telegram warns: "We cannot protect you from your own mother if she takes your unlocked phone without a passcode. Or from your IT department if they access your computer at work. Or from any other people that get physical or root access to your phones or computers." Right now, when it comes to ease of use and features, Messenger beats WhatsApp. But that's about to change. WhatsApp plans to introduce genuine multi-platform access with linked devices, it also looks set to add encrypted cloud backups of some sort which will provide the central messaging history Messenger offers. Perhaps even more pertinently, WhatsApp will also become interoperable with Messenger some time soon. So you can switch to an end-to-end encrypted (by default platform) while still staying in touch with those that do not. Any major feature updates where secure platforms seek to match the usability of Messenger will always introduce potential risks. "I'd argue that with many of these apps it's not end-to-end in the true sense," infosec researcher Sean Wright tells me. "I say this since you can receive messages and the history of messages when logging into another device." That said, such risks are a world away from the issues with Messenger or Twitter or SMS, where there is no default end-to-end encryption at all. So, to all those still using Messenger because it's easy and familiar, you now have a choice. Stick with this lack of security for the next few years, or make a switch to a platform that offers almost all of the benefits while fixing the most serious problem. "Non encrypted messaging platforms are widely open to attack," says Moore, "and left vulnerable once exploits are located. We must start to educate people about the risks and start transitioning to privacy focused apps." For its part, Facebook told me it remains "very committed to making Messenger end-to-end encrypted by default," suggesting that there has been no delay as such, that the timing "is consistent with what we've said since the launch—that it's going to take time and we're committed to doing this right." The company also pointed me to its defense of such security in the wake of U.S. government pressure. "People should be able to communicate securely and privately with friends and loved ones without anyone—including Facebook—listening to or monitoring their conversations," the company's Jay Sullivan told a senate committee last year. "People should be able to send medical information, private financial or payment details, and other sensitive content with the confidence that it will not fall into the hands of identity thieves or others with malicious intent... Facebook is committed to making such private communications broadly available." But that default security is not in place today and will not be in place any time soon. When Messenger does end-to-end encrypt by default, this advice will change. But, until then, the advice is to seek a secure alternative. Facebook needs to overcome its technical hurdles—but while so many continue to use the app, any urgency will be limited. The best thing we can do is reward those apps—including WhatsApp—that put our security and privacy first, and refrain from using those that don't. |
| The importance of security, data encryption for cloud - TechTarget Posted: 28 Jul 2020 12:00 AM PDT  The frequency of cyber attacks continues to increase, especially in the education, banking, health and government sectors. One reason for the rise is the transition from storing data on local databases to cloud storage, which is connected via both wired and wireless technologies. While cloud platforms present a convenient way to store large databases that contain customer, employee, financial and sales records, hackers can exploit weaknesses in cloud computing systems and obtain unauthorized access by representing the packet as local traffic. Hackers target organizations not only with on-premises data centers but also those with environments hosted on cloud computing platforms. Unfortunately, strong firewall rules are not sufficient to protect critical data and provide the authentication and authorization required for operational safety and security. What is needed is a rigorous testing and security validation at the database and application level. It is crucial to protect data in storage when at rest, where the data remains on a device permanently, and in transit, when the data is moved from one location or network to another location/network. To complicate matters, hackers use modern tools and techniques to gain unauthorized access to the data within an organization, on the internet or stored in cloud computing services. Therefore, data encryption and authentication, implementation of SSL certificates and avoiding non-SSL connections are essential. Equally important are establishing policies that restrict unintended access to environments and regular validation of identity and access management. Realizing the benefits of encryption and authenticationData encryption protects sensitive and private data by scrambling text data blocks into a secret code. A decryption key is required to unscramble the encryption. Different algorithms, including DES, AES and RSA, twist the data into an unreadable format, called ciphertext. The ciphertext is transmitted to the receiver with public and private decryption keys to decrypt the data. The receiver decrypts the ciphertext using both keys to turn the ciphertext into readable format. Data authentication is a complex network communication mechanism that maintains the nonrepudiation and integrity of data. Common data authentication methods include:
Secure Sockets Layer (SSL) certificates provide data encryption using specific algorithms. These certificates ensure the security of data transmission from malicious activities and third-party software. Two types of mechanisms are used for encryption within the certificates: a public key and a private key. The public key is recognized by the server and encrypts the data. SSL keeps the data encrypted until the user finishes the communication process. The data can only be decrypted by the private key. If a hacker succeeds to hack the data during the communication process, the encryption will render the data useless. SSL is recommended as an international standard for secure data transmission over websites. Best practices for securing company and customer dataOrganizations can employ several proven approaches to secure their data when using cloud computing. They include:
Cybersecurity mistakesThe biggest cybersecurity misconception is companies think they are completely protected from attacks because they spent millions of dollars implementing security protocols. They forget that there are always vulnerabilities that leave them open to risk, which could result in unrecoverable damages. With the advent of cloud storage, many companies were led to believe that simply moving to the cloud guarantees data protection. And while it is certainly a safe place to store a company's confidential data, it is not an impenetrable fortress. Additionally, some companies stick with older technologies without updating to newer, more secure advancements, which leaves them still vulnerable to security risks. Companies can tap into innovative security aspects to help them mitigate security threats. Software-defined networks can provide automated security at the hardware level through routers and switches. Configuration management tools provide a convenient method to manage and automate security settings. It is time for companies investing in cloud computing systems to also invest in making their cybersecurity systems more safe, reliable and robust against cyber attacks. About the Author |
| You are subscribed to email updates from "location of encryption devices,mobile security encryption,what does it mean to encrypt my phone" - Google News. To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google, 1600 Amphitheatre Parkway, Mountain View, CA 94043, United States | |

Comments
Post a Comment