Getting started with Signal and other encrypted messaging apps - PCWorld
Getting started with Signal and other encrypted messaging apps - PCWorld |
- Getting started with Signal and other encrypted messaging apps - PCWorld
- What is the Signal messaging app and how does it work? – Bestgamingpro - Best gaming pro
- What Is Secure Email, and Should You Switch? - How-To Geek
| Getting started with Signal and other encrypted messaging apps - PCWorld Posted: 11 Mar 2021 03:00 AM PST Right now. That's always the best answer to the question, "When is it a good time to start using an encrypted messaging app like Signal?" Ever since Edward Snowden became the world's most famous whistle blower, concerns about digital privacy have been front and center, and apps like Signal can help protect the wary. But what is Signal and other encrypted messaging apps, and how do they work? How Signal provides secure messagingThere are several end-to-end encrypted messaging apps for both Android and iOS. The one we'll focus on here is Signal, which is developed by Signal Messenger LLC and funded by the Signal Technology Foundation, a non-profit foundation. Another option is WhatsApp, which is now owned by Facebook, and uses the same basic encryption scheme that was developed for Signal. Telegram is another popular choice with an optional encrypted messaging feature. This app started life in Russia, though Telegram now operates from the United Kingdom and its operations center is in Dubai. 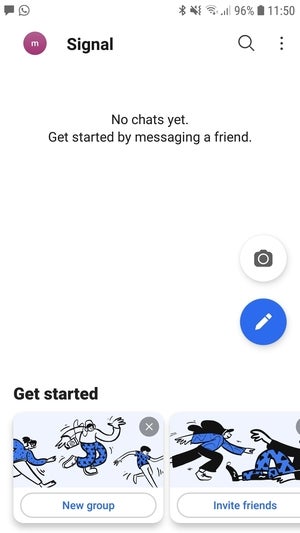 IDG IDG A freshly installed version of Signal. The common thread to all these apps? It's encryption, which just means your digital correspondence is scrambled to be indecipherable to third parties. The key selling point for these apps is that they use end-to-end encryption, which means the messages are encrypted on one device and then decrypted on another. Once encrypted, the message travels across the Internet, and only the person you're sending the message to can unscramble it. Even the servers that transmit those messages have no ability to see what they actually say. That is not the case with regular text messages, for example, or even regular email. Encrypted communication can be anything digital such as an email, a text, an image, a voice call, or a video chat. The other thing to note is that both sides of the transmission need to be using the same app. For example, you cannot send a message from WhatsApp and receive it in Signal. WhatsApp users communicate with other WhatsApp users and the same goes for Signal users. And so on. Why use encrypted messaging?Few of us are spies, political activists, or journalists working on high-stakes stories, so why would we want to use encrypted messaging in the first place? Well, despite claims to the contrary, the right to keep your own private business completely private is foundational to a free society. By extension, the ability to communicate with others without being spied on is critical for sharing personal views and ideas (whatever the subject) with others. It may not seem like you have anything critical to hide. But if you look through your texts and emails, you'll likely come across a lot of information that you wouldn't want others to know about. This can include meeting locations with friends, controversial opinions, your health status, vacation plans, and maybe even a credit card number or account password. Encrypted messaging: It's all about the keys Anton (CC0) Anton (CC0)Encrypted messaging uses a tool called "keys"—essentially long strings of letters and numbers. In their most basic form, these keys come in pairs: a public key and a private key. The public key is something that everyone can see and know about. A computer can then use this public key along with an encryption algorithm (fancy math!) to garble the message. Once it's garbled, the only way to read an encrypted message is to use the private key. Then when you respond to the encrypted message, the same thing happens in reverse. You use your friend's public key to encrypt a message, and when they receive the garbled text, they use their private key to unscramble it. The encryption schemes for messaging apps are now much more advanced than the original public-private key scheme. Signal's protocol, for example, uses a combination of permanent and temporary keys. The temporary keys are regenerated on a per-message basis to limit how much information would be exposed should the keys ever leak. On top of that, the temporary and permanent keys are combined (along with more fancy algorithms) to create additional shared secret keys between the two people communicating. With so many permanent, temporary, and shared keys required to read a single message, it becomes much harder for a third party to read these messages without direct access to one of the user's phones. So, that's how Signal does it. WhatsApp also uses Signal's encryption protocol for its messaging. Telegram, meanwhile, uses a proprietary encryption scheme. Even though encryption is far more complicated than it used to be, modern encryption apps are very easy to use. In the past, using encryption required at least some familiarity with the command line, and it often took several tries to work properly. And that was before you started managing your private key and figuring out how to use the encryptions keys with your email client. Then you had the additional problem of finding or convincing other people to go through this rigmarole, using complementary encryption tools on their end. With modern messaging apps, you may still need to convince your friends and family to begin using them, but that's the hardest part. There's no playing around with the command line and managing your keys manually because the app handles all the heavy lifting in the background. That simplicity, however, means that you must trust the app to behave as it claims (though that's true of all software). Installing SignalWe'll use Signal to walk through the installation process, but the steps aren't that different for both WhatsApp and Telegram. The first step is to download and install the app from Apple's App Store or Google Play. 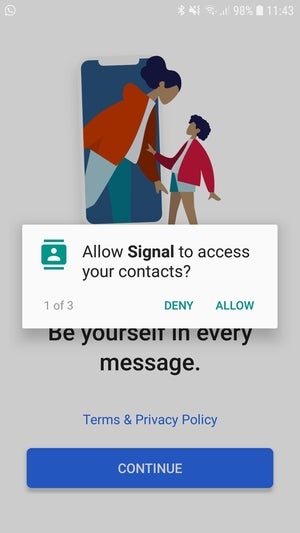 IDG IDG Signal needs access to your contacts to work. Next, when you open the app for the first time, it will ask for permission to access your contacts and media. Signal needs your contacts to see who among your friends uses Signal already, and the same goes for WhatsApp and Telegram. You can read about how Signal handles your contacts on its help pages, but in short Signal says it doesn't upload your actual contact names but rather "hashes" a string of letters and numbers that it uses to match with its other users. WhatsApp also uses hashing, while Telegram uploads your contacts but allows you to delete these records from its servers. Signal also asks for access your media and files so that you can send photos and files to your contacts. Next, Signal asks you to input your phone number, and then a text message is sent to your phone with a confirmation code to verify the phone number is yours. Then you're asked to create a user name (usually just your real name) and you can add an image if you like. Finally, you create a PIN for extra privacy, and that's it. Signal is ready to use. To send your first message, tap the pencil icon on the main screen, and if any of your contacts are using Signal their names will pop up in an alphabetized list. Select your contact and send them a text or start a voice call just as you would with any other messaging platform. In addition to one-on-one chats, Signal and WhatsApp support group text chats, voice calls, and video calls. Telegram supports voice calls and video calls, but its group text chats are not end-to-end encrypted. Understanding the limits of encrypted messaging Encrypted messaging apps are a good first step for securing your communications, but they're not a perfect solution. First, your messages are readable on your device, meaning if someone else has access to your unlocked phone, they will be able to see your messages. There are steps you can take to improve this. Signal, Telegram, and WhatsApp can all be set to require a fingerprint scan before allowing access to the app (assuming your phone has a fingerprint scanner). Another option is to regularly delete your messages, or at least the sensitive ones, to prevent them from being read. That only covers your end though, as your contacts will still have the conversation saved on their phone. Signal, WhatsApp, and Telegram also have a feature that automatically deletes messages on both ends. Automatic deletion does not, however, stop anyone from taking a screenshot of a conversation before it disappears. Potential security issues don't end there, either. Your phone itself can present security holes for keeping messages safe, especially on Android. This forum discussion, for example, noted that phones with specialized third-party keyboards may not be secure, as the keyboards themselves could be compromised by a government or malicious actor. While that isn't a problem with Signal itself, it is a potential loophole that could expose communications to bad actors, despite the use of a secure messaging app. Signal also has a support article about this issue. For WhatsApp, there's also the question of using a platform controlled by Facebook. The recent brouhaha over WhatsApp's terms of service changes turned out to be not quite what was feared. Nevertheless, there's still the chance that more and more information from WhatsApp will be turned over to Facebook in the coming years. To see what information is currently shared with Facebook from WhatsApp, check out this FAQ on the WhatsApp site. While there are downsides, most people can benefit from apps like Signal, WhatsApp, and others. Encrypted messaging services are a great way to keep private information private with apps that are very easy to use. Note: When you purchase something after clicking links in our articles, we may earn a small commission. Read our affiliate link policy for more details. |
| What is the Signal messaging app and how does it work? – Bestgamingpro - Best gaming pro Posted: 11 Mar 2021 04:30 AM PST Proper now. That's all the time the very best reply to the query, "When is it time to begin utilizing an encrypted messaging app like Sign?" Ever since Edward Snowden grew to become the world's most well-known whistle blower, issues about digital privateness have been entrance and heart, and apps like Sign may also help defend the cautious. However what's Sign and different encrypted messaging apps, and the way do they work? How Sign offers safe messagingThere are a number of end-to-end encrypted messaging apps for each Android and iOS. The one we'll deal with right here is Signal, which is developed by Sign Messenger LLC and funded by the Sign Know-how Basis, a non-profit basis. An alternative choice is WhatsApp, which is now owned by Fb, and makes use of the identical primary encryption scheme that was developed for Sign. Telegram is one other in style selection with an optionally available encrypted messaging function. This app began life in Russia, although Telegram now operates from the UK and its operations heart is in Dubai. 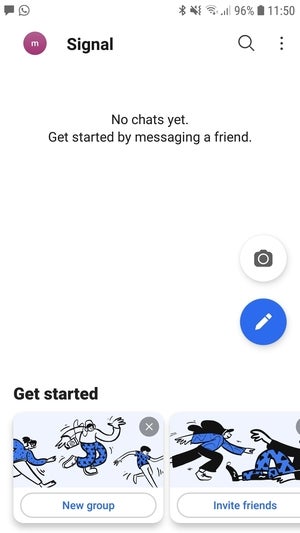 IDG IDG A freshly put in model of Sign. The widespread thread to all these apps? It's encryption, which simply means your digital correspondence is scrambled to be indecipherable to 3rd events. The important thing promoting level for these apps is that they use end-to-end encryption, which implies the messages are encrypted on one machine after which decrypted on one other. As soon as encrypted, the message travels throughout the Web, and solely the particular person you're sending the message to can unscramble it. Even the servers that transmit these messages don't have any capability to see what they really say. That isn't the case with common textual content messages, for instance, and even common e mail. Encrypted communication could be something digital comparable to an e mail, a textual content, a picture, a voice name, or a video chat. The opposite factor to notice is that each side of the transmission should be utilizing the identical app. For instance, you can not ship a message from WhatsApp and obtain it in Sign. WhatsApp customers talk with different WhatsApp customers and the identical goes for Sign customers. And so forth. Why use encrypted messaging?Few of us are spies, political activists, or journalists engaged on high-stakes tales, so why would we need to use encrypted messaging within the first place? Effectively, regardless of claims on the contrary, the proper to maintain your individual non-public enterprise fully non-public is foundational to a free society. By extension, the power to speak with others with out being spied on is crucial for sharing private views and concepts (regardless of the topic) with others. It might not appear to be you've got something crucial to cover. However in case you look by your texts and emails, you'll possible come throughout numerous info that you just wouldn't need others to learn about. This will embody assembly areas with pals, controversial opinions, your well being standing, trip plans, and perhaps even a bank card quantity or account password. Encrypted messaging: It's all concerning the keys Anton (CC0) Anton (CC0)Encrypted messaging makes use of a device known as "keys"—primarily lengthy strings of letters and numbers. Of their most elementary kind, these keys are available pairs: a public key and a personal key. The general public secret's one thing that everybody can see and learn about. A pc can then use this public key together with an encryption algorithm (fancy math!) to garble the message. As soon as it's garbled, the one method to learn an encrypted message is to make use of the non-public key. Then if you reply to the encrypted message, the identical factor occurs in reverse. You employ your pal's public key to encrypt a message, and once they obtain the garbled textual content, they use their non-public key to unscramble it. The encryption schemes for messaging apps at the moment are far more superior than the unique public-private key scheme. Signal's protocol, for instance, makes use of a mix of everlasting and short-term keys. The short-term keys are regenerated on a per-message foundation to restrict how a lot info could be uncovered ought to the keys ever leak. On prime of that, the short-term and everlasting keys are mixed (together with extra fancy algorithms) to create further shared secret keys between the 2 folks speaking. With so many everlasting, short-term, and shared keys required to learn a single message, it turns into a lot more durable for a 3rd get together to learn these messages with out direct entry to one of many person's telephones. So, that's how Sign does it. WhatsApp also uses Signal's encryption protocol for its messaging. Telegram, in the meantime, makes use of a proprietary encryption scheme. Although encryption is much extra difficult than it was, trendy encryption apps are very straightforward to make use of. Prior to now, utilizing encryption required no less than some familiarity with the command line, and it typically took a number of tries to work correctly. And that was earlier than you began managing your non-public key and determining learn how to use the encryptions keys together with your e mail shopper. Then you definitely had the extra downside of discovering or convincing different folks to undergo this rigmarole, utilizing complementary encryption instruments on their finish. With trendy messaging apps, you should still have to persuade your family and friends to start utilizing them, however that's the toughest half. There's no enjoying round with the command line and managing your keys manually as a result of the app handles all of the heavy lifting within the background. That simplicity, nonetheless, signifies that it's essential to belief the app to behave because it claims (although that's true of all software program). Putting in SignWe'll use Sign to stroll by the set up course of, however the steps aren't that completely different for each WhatsApp and Telegram. Step one is to obtain and set up the app from Apple's App Retailer or Google Play. 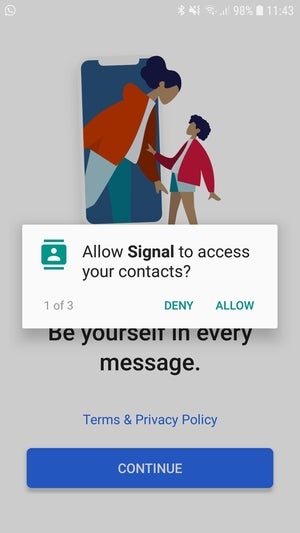 IDG IDG Sign wants entry to your contacts to work. Subsequent, if you open the app for the primary time, it's going to ask for permission to entry your contacts and media. Sign wants your contacts to see who amongst your mates makes use of Sign already, and the identical goes for WhatsApp and Telegram. You'll be able to examine how Sign handles your contacts on its assist pages, however in brief Signal says it doesn't upload your actual contact names however moderately "hashes" a string of letters and numbers that it makes use of to match with its different customers. WhatsApp also uses hashing, whereas Telegram uploads your contacts however lets you delete these information from its servers. Sign additionally asks for entry your media and information to be able to ship images and information to your contacts. Subsequent, Sign asks you to enter your telephone quantity, after which a textual content message is shipped to your telephone with a affirmation code to confirm the telephone quantity is yours. Then you definitely're requested to create a person identify (normally simply your actual identify) and you may add a picture in case you like. Lastly, you create a PIN for additional privateness, and that's it. Sign is able to use. To ship your first message, faucet the pencil icon on the principle display, and if any of your contacts are utilizing Sign their names will pop up in an alphabetized listing. Choose your contact and ship them a textual content or begin a voice name simply as you'll with some other messaging platform. Along with one-on-one chats, Sign and WhatsApp assist group textual content chats, voice calls, and video calls. Telegram helps voice calls and video calls, however its group textual content chats will not be end-to-end encrypted. Understanding the boundaries of encrypted messaging Encrypted messaging apps are first step for securing your communications, however they're not an ideal answer. First, your messages are readable in your machine, that means if another person has entry to your unlocked telephone, they are going to be capable to see your messages. There are steps you possibly can take to enhance this. Sign, Telegram, and WhatsApp can all be set to require a fingerprint scan earlier than permitting entry to the app (assuming your telephone has a fingerprint scanner). An alternative choice is to usually delete your messages, or no less than the delicate ones, to stop them from being learn. That solely covers your finish although, as your contacts will nonetheless have the dialog saved on their telephone. Signal, WhatsApp, and Telegram even have a function that mechanically deletes messages on each ends. Computerized deletion doesn't, nonetheless, cease anybody from taking a screenshot of a dialog earlier than it disappears. Potential safety points don't finish there, both. Your telephone itself can current safety holes for protecting messages secure, particularly on Android. This forum discussion, for instance, famous that telephones with specialised third-party keyboards is probably not safe, because the keyboards themselves could possibly be compromised by a authorities or malicious actor. Whereas that isn't an issue with Sign itself, it's a potential loophole that would expose communications to unhealthy actors, regardless of using a safe messaging app. Sign additionally has a support article about this issue. For WhatsApp, there's additionally the query of utilizing a platform managed by Fb. The current brouhaha over WhatsApp's terms of service changes turned out to be not fairly what was feared. Nonetheless, there's nonetheless the possibility that an increasing number of info from WhatsApp shall be turned over to Fb within the coming years. To see what info is at present shared with Fb from WhatsApp, take a look at this FAQ on the WhatsApp site. Whereas there are downsides, most individuals can profit from apps like Sign, WhatsApp, and others. Encrypted messaging providers are an effective way to maintain non-public info non-public with apps which can be very straightforward to make use of. Word: Whenever you buy one thing after clicking hyperlinks in our articles, we could earn a small fee. Learn our affiliate hyperlink coverage for extra particulars. |
| What Is Secure Email, and Should You Switch? - How-To Geek Posted: 11 Mar 2021 03:40 AM PST  Email was invented in 1971 and has changed very little since then. In that time, it's managed to become a major security risk to individuals, governments, and private companies around the world. This might explain the rising popularity of so-called "secure email" providers. So what exactly makes secure email different from regular email? What Is Secure, Encrypted Email?Secure email is essentially regular email with a few security enhancements on top. The technology behind the scenes is ultimately the same, which means that you already know how to use a secure email provider. You still send messages to named addresses with an @ and a domain, and you still get plenty of spam. For that reason, anyone can call themselves a secure email provider. There's no dictionary definition, and most major email providers like Gmail and Outlook would also consider themselves "secure" despite falling short of the mark. Most providers who use the term to describe their service go much further than requiring a strong password or using two-factor authentication. Security, in this sense, isn't only about stopping someone from gaining access to your account, it's also about keeping your data and identity safe. A truly secure email provider is unable to read your email conversations. They should ideally be located in a jurisdiction that's not subject to data sharing between intelligence agencies. The technology itself would ideally be built on open standards for a "crowdsourced" approach to security. The service shouldn't profile you, serve personalized ads, or log metadata. This is why Gmail, Outlook, Yahoo, and most other free, mainstream email providers are not regarded as being truly secure. A secure email provider is "better" than Gmail in terms of data security, but you will miss out on Google's features and deep integrations. Let your priorities decide which is the better option. How Do Secure Email Providers Protect You?End-to-end encryption is essential in building a truly secure email system. While services like Gmail encrypt the connection between your computer and the server, any information you send to the server (including the contents of your messages) is not encrypted when it gets there. Any private conversations (or state secrets) you're discussing will sit on Google's servers in an unencrypted format. If that data is stolen, for example, in a data leak, it doesn't need to be decrypted before it can be read. A secure provider will encrypt data on the server, making it useless to any third parties. The lack of end-to-end encryption means that email providers can access the contents of your messages, and they've used this access in the past. Google previously scanned the contents of Gmail messages for advertising purposes but stopped the practice in 2017. The company continued scanning email to power services like (the now-defunct) Google Now. How else will Google's assistant be able to remind you about the trip you've got coming up?
Where those servers are located could also impact how that data is treated. As is the case with VPNs, the most secure email services are usually located in remote or historically neutral countries. ProtonMail, for example, is located in Switzerland, where privacy laws are notoriously strict. Email services located in the United States can be challenged in court to hand over data. The United States is a part of the Five Eyes intelligence alliance, alongside Australia, Canada, the United Kingdom, and New Zealand. Data is routinely passed between different authorities in different jurisdictions under the guise of national security. The kind of data that is logged alongside your email can also say a lot about you. Metadata is essential "data about data," like timestamps on an email or the user agent "signature" left by the browser you are using. You don't consciously create metadata, but it serves as a paper trail for almost anything you do online. Secure email services will be sure to strip as much metadata out of the email being sent as possible. This makes it harder to trace the origin of a message and further protects the identity of the person sending it. Some secure email providers also integrate tools like Pretty Good Privacy (or PGP for short) into their interfaces. PGP lets you "lock" the contents of a message so that it can only be read by someone with the correct private key. When set up correctly, your email will look normal, as legible plain text. If someone without the key were to intercept the message, it would look like gibberish. Finally, there's an argument to be made for building security-focused products on open-source software. Source code that has been released to the public can be put to the test in a way that closed source code cannot. RELATED: What Is End-to-End Encryption, and Why Does It Matter? Which Secure Email Service Is the Best?There is no one-size-fits-all approach to secure email. There are many different providers, all offering differing levels of security at a variety of price points. Budget is something you will likely have to consider since most services do not offer a generous free option like Gmail or Outlook.com.
ProtonMail (free account available) is one of the best-known encrypted providers, and one of the most mature. Data is encrypted on servers located in Switzerland, with the company conducting audits to ensure that users can trust its protections. The service is built on open-source technology, and there's a dedicated mobile app for iPhone and Android (but no support for default mail apps, unfortunately). Tutanota (free account available) is another highly recommended secure email provider, with a feature set (and auditing) that's similar to ProtonMail. Servers are located in Germany (the company has explained why), and the service is built on many open-source foundations. There's a similar caveat with mobile access in that you need to use a dedicated app to decrypt your email.
Posteo (no free accounts) is also located in Germany and has made a bit of a name for itself for being a cheaper alternative to both ProtonMail and Tutanota. Everything is encrypted end-to-end, with support for PGP implementation to provide additional peace of mind. There's also no need for a name, backup email, or other identifying information to create an account. There are many other secure email providers to choose from (way too many to list here), including Mailfence, mailbox.org, Fastmail, and CounterMail. You should give some serious thought to the secure email service you choose, just as you would if you were picking a VPN. It's best to choose an established provider with a solid track record given the nature of this kind of service. One such Iceland-based provider, called UnSeen, disappeared without a trace in late 2020, only to reappear with a Taiwanese domain name, which has led to all sorts of speculation and distrust. Do You Need a Secure Email Provider?If you need a secure email provider, you probably already know it. Maybe you're a journalist and are worried about subpoenas exposing sources and private materials. Maybe you're the next Edward Snowden. For most people, a secure email provider probably isn't necessary. It will provide peace of mind at the cost of some features, convenience, and money. Your email provider won't be able to see the contents of your messages, and it will be easier to communicate with people with end-to-end encryption. (You could, of course, just use Signal to communicate with end-to-end encryption, too.) Whether that's worth it is up to you. But if your primary motivation is security, understand that you're more likely to fall victim to social engineering attacks than email data breaches. RELATED: What Is Signal, and Why Is Everyone Using It? |
| You are subscribed to email updates from "encrypted phone calls iphone,what does encrypt phone mean,what is encryption of phone" - Google News. To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google, 1600 Amphitheatre Parkway, Mountain View, CA 94043, United States | |
Comments
Post a Comment