iOS 13: Everything You Need to Know About Apple's Find My App - Mac Rumors
iOS 13: Everything You Need to Know About Apple's Find My App - Mac Rumors |
- iOS 13: Everything You Need to Know About Apple's Find My App - Mac Rumors
- How secure are Dropbox, OneDrive, Google Drive and iCloud? - https://proprivacy.com/
- Keepass review | Is this password manager secure? [in-depth review] - https://proprivacy.com/
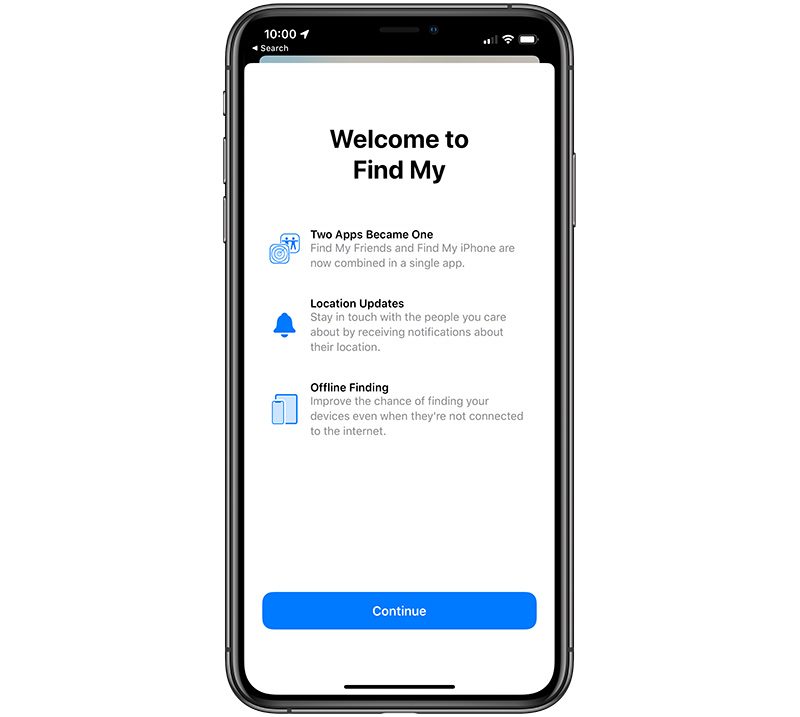
| iOS 13: Everything You Need to Know About Apple's Find My App - Mac Rumors Posted: 05 Jul 2019 12:32 PM PDT Apple in iOS 13 and iPadOS merged the Find My Friends and the Find My iPhone apps into one app that's just called "Find My," because, well, it's used for finding whatever you need to find. Find My works similarly to the Find My iPhone and Find My Friends apps that were previously available, but it has a nifty new feature that's designed to let you find your lost devices even when you don't have a WiFi or LTE connection. Note that this guide is designed to walk through all of the Find My features on iPhone and iPad, but it also applies to the Mac, which also has a new Find My app in macOS Catalina.
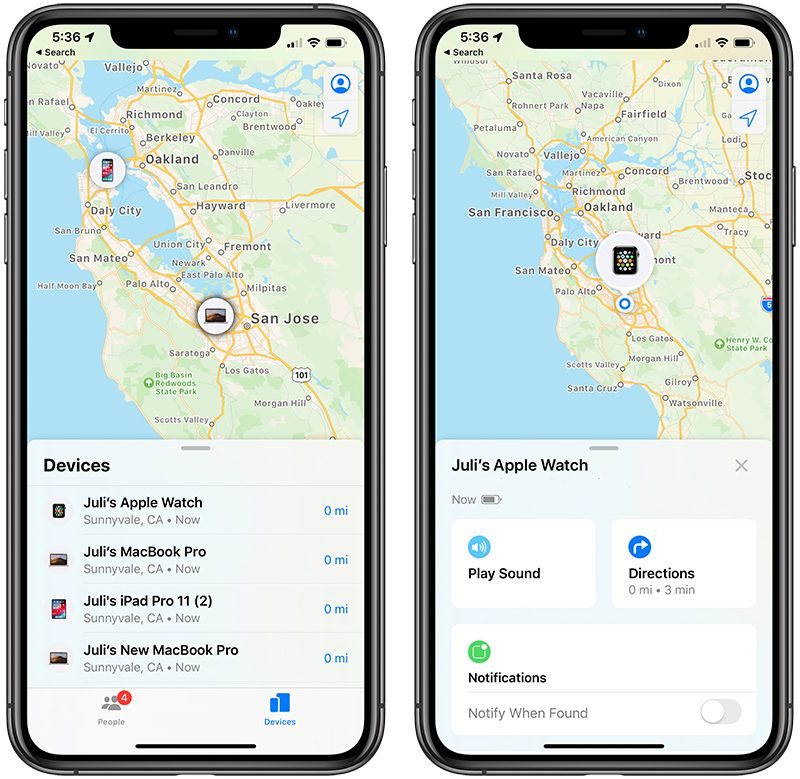
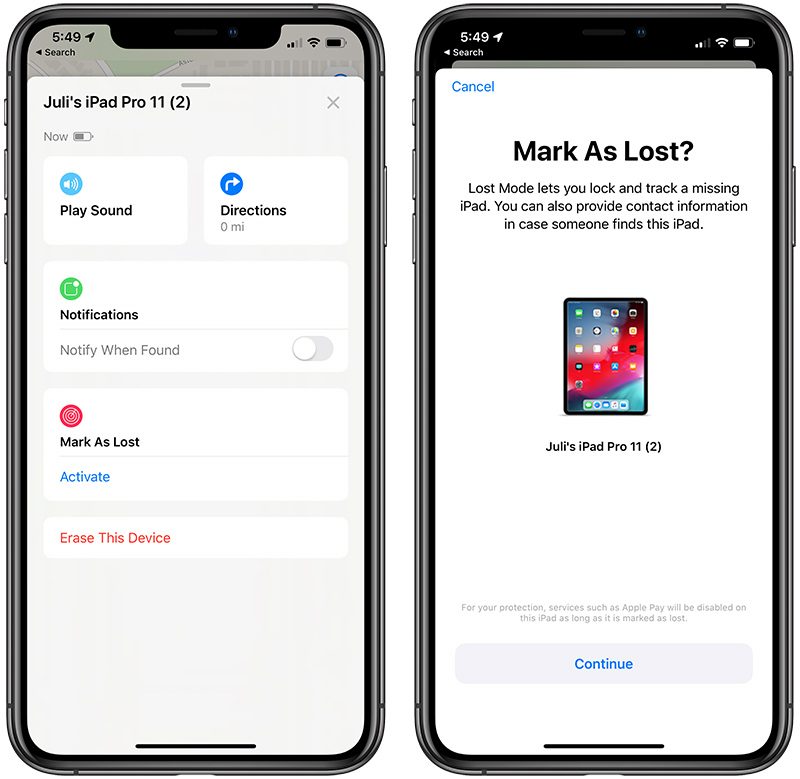
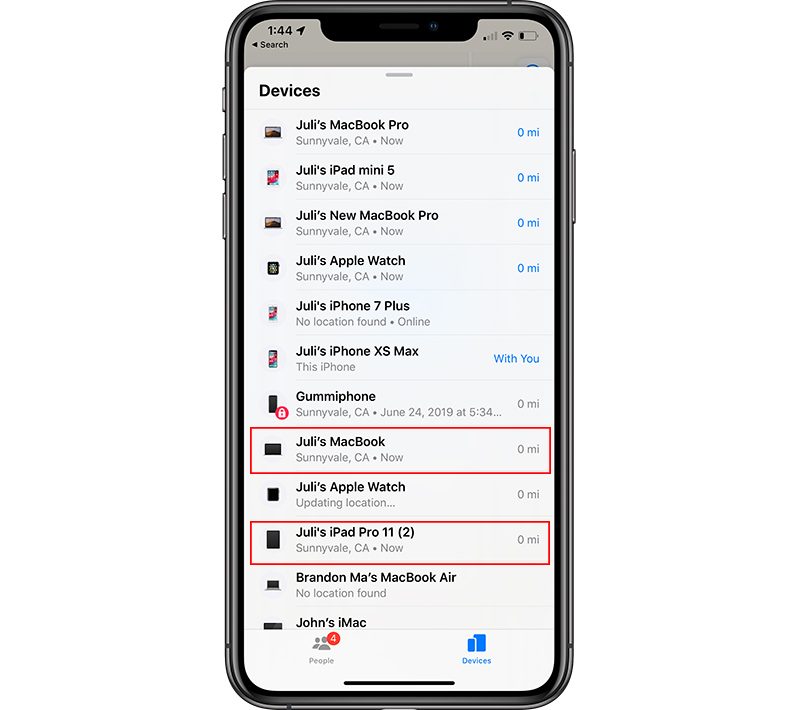
Locating Lost DevicesThe Find My app is organized into three sections, accessible by tapping the tabs at the bottom. On the left, you can find people, in the middle, you can find your own devices, and on the right, there's a "Me" tab introduced during the beta testing process. As with the prior Find My iPhone app, all of your Apple products are listed. Devices where you're signed into iCloud and have the Find My feature enabled will be locatable through the Find My app.
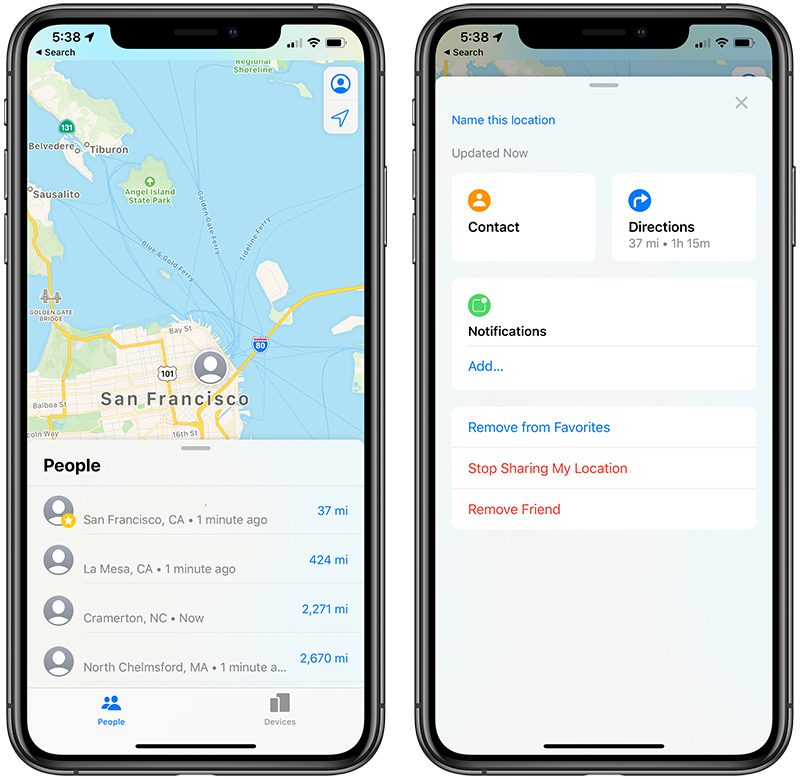
Find My Compatible DevicesAlmost all Apple products are Find My compatible, including iPhone, iPad, Macs, Apple Watch, and AirPods. Family SharingIf you have Family Sharing enabled, all of your family's devices will be listed in Find My right alongside your own, so you can also find devices from your partner or children through the Find My app. Locating FriendsThe Find My app allows you to locate friends and family members that have shared their location with you. You can view their location using the "People" tab within the Find My app. The Find My app lists people who have shared their location with you and, if you haven't shared your own location, offers up an option to do so.
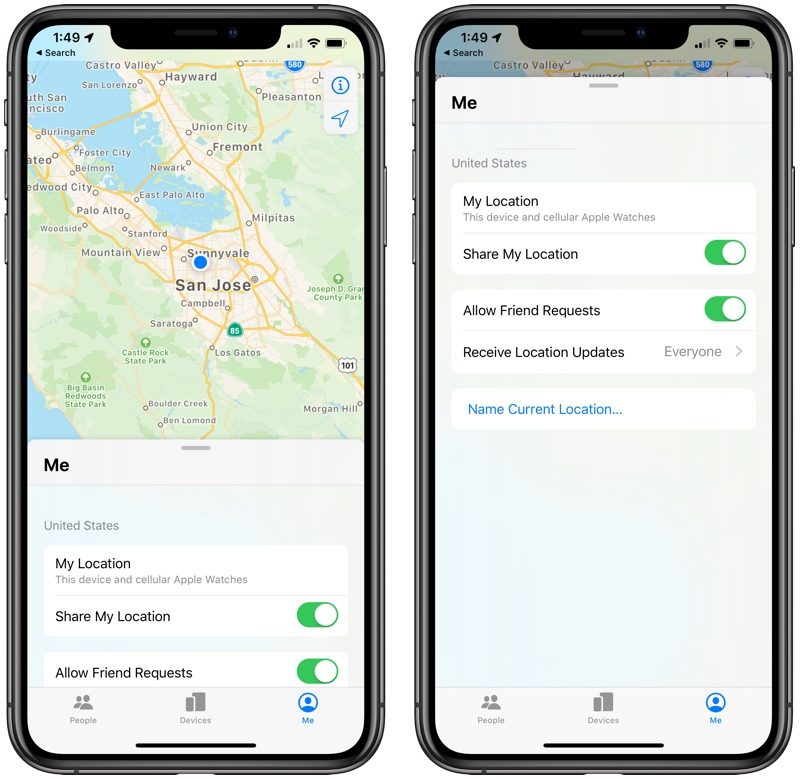
Sharing LocationIf you press the "Share My Location" button, you can share your own location with any of your contacts even if they haven't shared a location with you. Tapping on a person's name in the list provides an option to bring up their Contacts card for sending a message or an option to get directions to their location. You'll also find tools for removing friends and turning off your own location sharing with the person if it's a mutual location sharing contact. You can opt to share your own location permanently, for an hour, or until the end of the day. NotificationsFor any person who's sharing a location with you, you can turn on notifications to get notifications when they leave or arrive at a specific location. There's also an option to notify your friend when you leave or arrive at a specific notification. Me TabThe "Me" tab in the Find My app displays your current location and includes toggles for sharing location, allowing friend requests, choosing who to receive location updates from, and naming a specific place.
Locating Devices Without a ConnectionOne of the headline features of iOS 13 is a new Find My option that lets your lost devices be located even when not connected to WiFi or LTE by leveraging Bluetooth and proximity to other nearby Apple devices. When your lost device is offline but close to another device, it's able to connect to that other device over Bluetooth and relay its location. That means that your devices are more trackable than ever, and there's a better chance you can find a device that's been lost.
Tracking a device in this way requires Bluetooth to be enabled because location is shared with another device using Bluetooth. Turning off Bluetooth or power makes your device untrackable, but if it's on, has Bluetooth, and is near another Apple device, it will potentially be trackable even if it can't connect to WiFi or LTE. You're not going to notice a difference in the Find My app when tracking a device over Bluetooth rather than a cellular or WiFi connection -- it simply shows up in the list of devices like any other device that does have a standard connection. Offline devices do have their distance from you listed in gray instead of blue, and you can tell when the location data was last updated by the time listed. In testing, setting an iPad into Airplane mode and enabling Bluetooth continued to allow the iPad to be tracked thanks to another nearby iPhone, but turning off Bluetooth prevented it from being found even from a device to device connection. How It WorksImplementing the device to device location feature while preserving privacy was quite a feat and the technical details of how it works are quite complicated, but Apple has given a high level overview of how it functions. Basically, it's been designed with an encryption system that prevents people from abusing the feature for doing things like tracking you. That encryption system makes your personal location unavailable to people aiming to intercept your device's Bluetooth signal and from Apple itself. Find My requires Apple users to have at least two devices. Each of your devices emits a constantly changing public key that nearby Apple devices pick up, encrypt, and upload with your geolocation data. To decrypt that location signal, you need a second Apple device logged in with your Apple ID credentials and protected with two-factor authentication. Essentially, only your own devices can decrypt the encrypted location signal that's being sent from a lost device, no one, not even Apple, can intercept it and locate you or your devices. As an example scenario, if you were on an airplane, had your iPhone in Airplane Mode with Bluetooth on, and then left it behind on the plane accidentally, it would potentially still be trackable. In this situation, a flight attendant or an airport worker with an iPhone might come across it. The flight attendant's own iPhone would connect to your lost iPhone over Bluetooth by picking up your public key. The flight attendant's iPhone would then upload your device's encrypted location and a hash of your public key (for identification purposes) to Apple's servers, where one of your own devices will be able to receive the encrypted info and decrypt it to make the offline device able to be tracked. PrivacyBecause the entire Find My system is end-to-end encrypted, other people can't get the location of your devices using Bluetooth, nor can Apple. Lost devices are trackable only by you. Device ImpactAccording to Apple, Find My's background Bluetooth location tracking feature uses just tiny bits of data piggybacked on existing network traffic so there's no impact on device battery life, data usage, or privacy. Find My RumorsRumors have suggested Apple plans to expand Find My's functionality through the introduction of a new hardware product that's similar to the Tile Bluetooth item tracker. Apple is said to be working on a tag that can be attached to any item that would allow it to be tracked. Like Tile, Apple's rumored tracker reportedly lets users receive a notification when a device gets too far from the tag, potentially cutting down on lost items. Guide FeedbackHave questions about Find My, know of a feature we left out, or want to offer feedback on this guide? Send us an email here. |
| How secure are Dropbox, OneDrive, Google Drive and iCloud? - https://proprivacy.com/ Posted: 05 Jul 2019 08:11 AM PDT  These days we all have huge amounts of text documents, songs, photos, videos, and other personal data that we want to protect. Storing our data locally can be risky because a hard drive can become corrupt, and a mobile device could be lost, stolen, or broken. Reports have even surfaced of people losing their entire photo collection when they update their Windows operating system, much to their despair. Storing data online is an excellent way to protect against this kind of loss, but, is cloud storage secure? When it comes to backing up data online, there are several key services that people tend to use. These being; Google Drive, Dropbox, OneDrive, and iCloud. In this article, we will look at these popular storage services and review how secure these cloud storage services actually are. Is Google Drive secure?Google Drive is an easy and efficient way to back up data to the cloud, and, because it is available for free (up to 5GB of storage) with a Gmail account, it is extremely popular. For people backing up sensitive documents, however, concerns may exist about how secure Google Drive really is. After all, evidence has previously surfaced of Google working hand in hand with the NSA on its PRISM surveillance program. So, what kind of security does Google Drive really provide? If you are considering Google Drive as an option, see our Google Drive review. In TransitThe first possible security risk for your data is during transmission. When you upload your data to Google's central servers, it must travel there via the internet which means that it could be intercepted while in transit. To mitigate against this, Google encrypts your data using TLS before uploading your data. This is the same encryption standard used to secure browser connections to HTTPS websites. A quick check with the independent encryption auditing tool Qualys SSL Labs reveals that Google's TLS connections are rated A+ (which is as good as it gets). Google also encrypts your data whenever it is in transit within its internal network. This means that your data is always encrypted when it moves from one Google server to another, and during synchronization with your various devices. At RestOnce your data arrives with Google, it is encrypted in order to keep it secure within its cloud servers. Google uses 128-bit AES encryption for all data that is at rest. Although this is not as strong as 256-bit encryption; it is still considered future proof for the time being. For added security, Google encrypts the AES encryption keys used to encrypt your data with a rotating set of master keys. This adds an extra layer of security to the data stored on Google's servers. Google encrypts all your files "on the fly" to ensure that your data is always stored securely and that only the file you actually want to access is decrypted. However, Google holds the key to your files on your behalf, which means that the firm can go into your files if it wants to. Privacy policyGoogle's terms of service state that "you retain ownership of any intellectual property rights that you hold in that content. In short, what belongs to you stays yours." However, the firm does say that it has the right to use your private content to improve its services. This means the firm can scan your documents for information and keywords in order to better serve you ads (across its other services) - or to otherwise improve its services and develop new ones. Because Google asks for consent to access everything you upload, it cannot claim HIPAA compliance. Google also retains the right to hand over your data to the authorities if it is served a warrant. This means that the US government could get inside all your files and you would never know (due to gag orders). None of this is ideal and is the primary reason why any cloud storage service that does not provide end-to-end encryption it can never be considered truly secure. Is OneDrive secure?OneDrive is a popular cloud storage service provided by Microsoft. Like Google Drive, it gives users 5GB of free storage as soon as they sign up for a Microsoft account. If you are a OneDrive user you may be wondering just how secure your data is. So, let's take a look… In transitData that is transmitted to Microsoft's OneDrive cloud storage is encrypted with TLS encryption using 2048-bit keys. This is a robust encryption that ensures that your data is protected from hackers and tracking while in transit. In order to keep your data secure as it passes from one server to another (Microsoft stores your data in multiple locations to protect it against disasters), the firm also encrypts your data before moving it around internally. Microsoft states that although "data is already transmitted by using a private network, it is further protected with best-in-class encryption." At restWhile Microsoft definitively provides information about encryption at rest for paying "business" level users of OneDrive. Trying to find evidence of encryption at rest for free OneDrive users is trickier. Business users are told that BitLocker encrypts all the data they store on Microsoft's servers. Per-file encryption provides on-the-fly encryption for each individual file that you upload. According to Microsoft, it uses AES 256 encryption that is Federal Information Processing Standard (FIPS) 140-2 compliant. This is strong encryption. Despite the confusion surrounding the difference between business and personal accounts, we can only presume that Microsoft does indeed provide encryption at rest for all OneDrive users. This article certainly suggests that it is true: "Each file is encrypted at rest with a unique AES256 key. These unique keys are encrypted with a set of master keys that are stored in Azure Key Vault." That statement implies that all OneDrive users are getting at rest encryption and that this encryption is on-the-fly. (Though it would be nice if Microsoft made the difference between business and personal accounts absolutely clear). However, it is worth remembering that OneDrive is a completely proprietary cloud storage service. It is closed source, which means that it is impossible to verify how secure your data is. In addition, because the firm encrypts your data on your behalf - and it holds the encryption keys on its servers - it has the ability to access your data if it wants to and can scan your documents as it wishes. Privacy policyAs is the case with Google's services, Microsoft's OneDrive is covered by a general privacy policy for all of Microsoft's products and services. This policy states that Microsoft has the right to access your data in order to better provide its services. It also allows the firm to access your data for the purposes of tracking and serving adverts. Microsoft's policy also reminds users that it will comply with government warrants if it is asked to: "Finally, we will access, disclose and preserve personal data, including your content (such as the content of your emails, other private communications or files in private folders), when we have a good faith belief that doing so is necessary to: 1.comply with applicable law or respond to valid legal process, including from law enforcement or other government agencies." Meaning, your data could be accessed by the authorities at any time, and because the US enforces gag orders - you would never be notified about this intrusion into your data. Thus, as is always the case, if you want your data to be stored online securely it is vital to opt for a service that provides true end-to-end encryption (and that is open source). Is iCloud secure?iCloud is Apple's cloud storage service. As it is Apple's home-cooked service that is baked into its products, it is an extremely popular service among Apple users. It is often assumed to be good for privacy and more secure than some of its competitors. However, like the other popular services in this article, iCloud is closed source. This means that its source code is not available to be audited by security professionals. So you just have to trust Apple to provide the level of security that it claims. Apple was previously revealed (by Edward Snowden) to have worked hand in hand with the NSA to snoop on its users. So, can you trust it? And is Apple's iCloud really more secure than its competitors? In TransitIn 2014, Apple received a lot of bad press after a string of attacks on iCloud users. According to those reports, connections to iCloud servers were vulnerable to a man in the middle attack. Apple denied this, claiming that victims had actually been phished. Despite this, the firm has made improvements to the security of its iCloud service. Apple states that all communication with iCloud servers is protected with TLS 1.2 encryption with Forward Secrecy. We checked iCloud's TLS security using Qualys SSL Labs and were happy to find that the service gets an A+. Thus, the security of data in transit should be fine. For additional security, when you access iCloud services using native Apple apps such as Mail, Calendar, or Contacts, authentication is handled using a secure token. Secure tokens eliminate the need to store your iCloud password on your device or computer. Unlike a password (which could be used to sign in from a different device) that token can't be stolen because it is cryptographically tied to your device (and without the device it is useless). We were also unable to verify what kind of protection Apple uses to pass data around its private networks. One would presume that the firm does use encryption to pass data between cloud servers, but information on the level of security is not freely available. At restApple states that all data is stored on its servers using AES 128 encryption. This is not as secure as the AES 256 encryption provided by many cloud storage services but is still considered future proof for the time being End-to-end encryption is available for some data that is communicated to Apple's servers (Apple uses end-to-end encryption for iMessages and FaceTime, and for home data, health data, iCloud Keychain, payment information, Quicktype keyboard learned vocabulary, screen time, Siri information, and Wi-Fi network information). However, it is not available for individual files transmitted to iCloud. This means that Apple retains control over the encryption keys for the files it encrypts on your behalf on its cloud storage. This is far from ideal, because it means that the keys to your data could be accessed by Apple staff, leaked online, or perhaps even hacked from its servers by cybercriminals. Privacy policyApple's privacy policy makes it clear that iCloud user data may be accessed under some circumstances: "We also use personal information to help us create, develop, operate, deliver, and improve our products, services, content and advertising, and for loss prevention and anti-fraud purposes. We may also use your personal information for account and network security purposes, including in order to protect our services for the benefit of all our users, and pre-screening or scanning uploaded content for potentially illegal content, including child sexual exploitation material." As you can see, the policy allows Apple to scan your documents to ensure that they are not illegal. It is unclear if Apple uses its ability to scan documents for any other purposes, but it does also give itself permission to use people's data for developing new services. So, it seems likely that it is performing some level of corporate espionage. Of course, as Apple is closed source, it is impossible to verify exactly what kind of snooping might be occurring. As is the case with Google and Microsoft, Apple's policy also states that it will comply with legal requests for data. This means it is possible that the firm could be served a gag order and your iCloud data could be accessed without your knowledge: "It may be necessary − by law, legal process, litigation, and/or requests from public and governmental authorities within or outside your country of residence − for Apple to disclose your personal information. We may also disclose information about you if we determine that for purposes of national security, law enforcement, or other issues of public importance, disclosure is necessary or appropriate." So, how often are Apple actually going into people's accounts? In the first half of 2015, Apple admitted to getting 4,472 requests from police authorities around the world. Apple states that it disclosed data to police for 1,886 of those requests (of which 1,407 were provided to US law enforcement). Finally, it is also worth noting that Notes stored on iCloud are never encrypted, ever. Is Dropbox secure?Dropbox is a cloud storage service based in San Francisco, California. It is the only cloud storage service on this list that does not belong to a tech giant, instead, it has risen to popularity on the strength of its service alone. Despite this, it is hard to consider Dropbox more secure than the other popular competitors in this article. In fact, the service has been directly criticized by Edward Snowden, who has been very vocal about the lack of privacy that users get on the platform. Dropbox is partly GPLv2 license and partly closed source. This means that it is impossible to independently verify all the source code for the service. This is enough to put some people off the service because there are fully open source cloud storage services on the market. In TransitAs is the case with the other services mentioned in this list, Dropbox uses secure TLS to protect all data that is passed from consumers to company servers. Dropbox states that its TLS connections create a tunnel that is protected with AES 128 encryption. We checked Dropbox services with Qualys SSL Labs to see whether it passes the independent auditor's tests. Qualys rated the TLS connection with an A+ which means that those connections can be trusted to protect user data while it is in transit. However, Dropbox does not provide end-to-end encryption, which means that data is still susceptible to the possibility of being intercepted. At restDropbox stores all data on its servers with strong AES 256 encryption. However, it is impossible to tell from its own publications whether that encryption is provided on-the-fly for each file that is accessed. As is the case with the other services in this article, Dropbox does not provide end-to-end encryption. Instead, it holds the encryption keys for everybody's data and retains full control over the encryption and decryption of data on behalf of the user. This is a risk in terms of security and privacy because it means that the firm can access user data whenever it wants to. In addition, it is possible that user data could be exposed if there is an internal leak or if hackers manage to steal users' encryption keys from the company's servers. It is also worth noting that the service has previously suffered problems with its authentication mechanisms, as a result of which anyone could access everybody's Dropbox files for around four hours - without the need for an account's password. In addition, security researchers previously discovered a fault in the Dropbox iOS app which was storing user login information in plain text. However, it has since fixed those problems and has added security measures to allow consumers to protect their accounts. These include dual-factor authentication, a page to check active logins to the account, automated systems that check for unusual activity, and forced password updates for accounts that are thought to be acting suspiciously. Despite these improvements, anybody wanting to use Dropbox in a completely secure manner will need to use third-party software to encrypt their data before uploading it to Dropbox. Privacy policyThe Dropbox privacy policy clearly states that your data will always remain yours. However, the policy does give the firm permission to "scan" all your data for the reason of better providing its services: "When you use our Services, you provide us with things like your files, content, messages, contacts, and so on ("Your Stuff"). Your Stuff is yours. These Terms don't give us any rights to Your Stuff except for the limited rights that enable us to offer the Services. We need your permission to do things like hosting Your Stuff, backing it up, and sharing it when you ask us to. Our Services also provide you with features like photo thumbnails, document previews, commenting, easy sorting, editing, sharing, and searching. These and other features may require our systems to access, store, and scan Your Stuff." As if that wasn't enough, signing up to Dropbox also means that your data could be shared with third parties: "You give us permission to do those things, and this permission extends to our affiliates and trusted third parties we work with." Being a US firm, also means that Dropbox could be served a warrant and gag order. Under such circumstances, the US government could gain access to anybody's data, indefinitely. Due to the gag order, users would never know that US intelligence agencies were performing surveillance on the contents of people's accounts. Dropbox makes it clear that it will comply with legal requests and warns users that they should not use their accounts to share copyrighted content: "You're responsible for your conduct. Your Stuff and you must comply with our Acceptable Use Policy. Content in the Services may be protected by others' intellectual property rights. Please don't copy, upload, download, or share content unless you have the right to do so." The policy makes it clear that privacy is not assured using the service. Your content will be scanned and could be used to prosecute you if you are found guilty of breaking any laws including copyright piracy. Best practices for using cloud storageAs you can see from this article, there are many questions surrounding the data privacy provided by popular cloud storage services. No end-to-end encryption means that you must trust the provider to store your data and protect it. And, due to their base in the US, there is always the possibility that the government could infiltrate the data in those accounts using a gag order. Whether the cloud storage services above are an acceptable solution for you largely depends on your personal circumstances. If allowing Google, Apple, Microsoft, or Dropbox, to store your documents encrypted on your behalf seems secure enough for you, then, by all means, use those services. However, if you truly value privacy it is always going to be better to seek out open source alternatives with end-to-end encryption. If you do decide to use one of the services above, there are certain best practices that we recommend:
|
| Keepass review | Is this password manager secure? [in-depth review] - https://proprivacy.com/ Posted: 05 Jul 2019 08:38 AM PDT KeePass is a free and open-source (FOSS) password manager. It is a Windows program, but versions of it are available for all platforms including macOS, iOS, Android, and Linux. KeePass is not hard to use, but it lacks the slick user interfaces offered by many of its commercial rivals. Syncing across devices also take a little more work than with most password manager apps, but there is a good reason for this. KeePass uses true end-to-end encryption. You create encrypted KeePass (.kdbx) files that, by default, never leave the device they are created on. They are not stored on a centralized database that can be hacked (as commercial password manger ones often are), and only you hold the encryption keys to them. The main downside of this, of course, is that there is no safety net - no third party that can bail you out if you forget your master password! KeePass supports a selection of plugins that extend its functionality far beyond that of any other password manager. Please note that this article concerns KeePass 2.x. (2.42 at time of writing). KeePass 1.x is a fundamentally different program which remains maintained primarily for backward compatibility reasons. We can see no advantage whatsoever in using KeePass 1.x unless you need to work with legacy password files. Pros
Cons
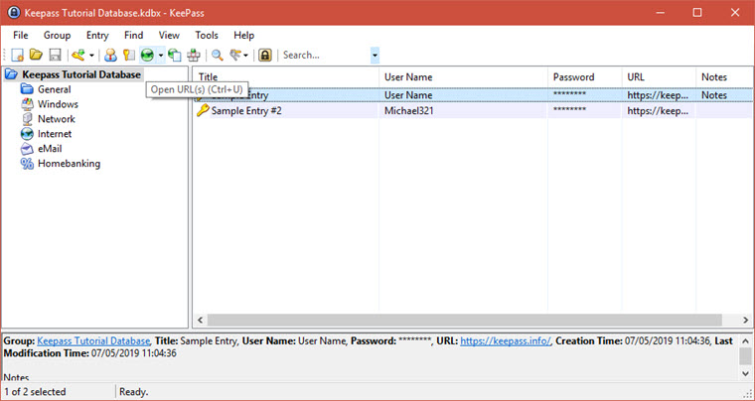
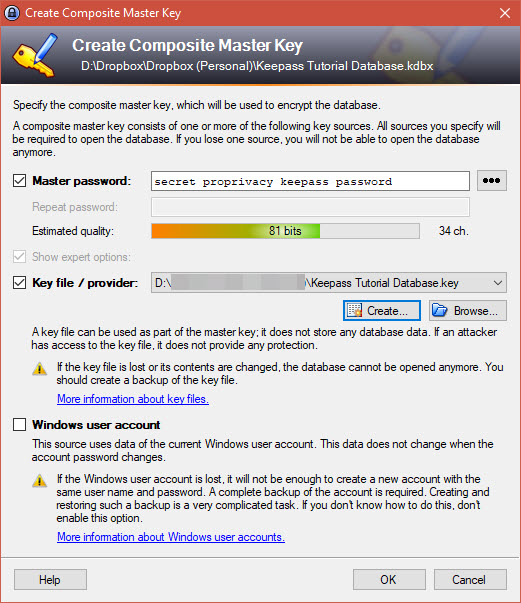
KeePass pricingKeyPass is community developed, free and open source software (FOSS). It doesn't cost a penny. There are no commercial versions of it. Features
Additional features are available via a huge list of plugins and extensions, many of which cater to rather niche requirements. Cross-platform and syncPasswords are stored inside encrypted KeePass containers, often referred to as .kbdx files after their file extension. These .kbdx files can be securely stored anywhere, including insecure locations such as Dropbox and Google Drive. The ability to store .kbdx files safely in the cloud is very handy for syncing across devices, as KeePass-compatible apps on any platform can access and open the files with the correct password (and key file and/or other 2FA if used), modify them, and save the updated version to the cloud location. This allows for seamless e2ee syncing across devices and platforms. The only kink being that, thanks to the locked-down nature of iOS apps, KeePass apps in iOS must import and export .kbdx files from the iOS Dropbox app rather than simply opening and saving the file in Dropbox directly. This is admittedly a bit of a pain, but blame Apple, not KeePass. To see how KeePass works in Android, check out our Keepass2Android review. Privacy and securityOpen-sourceUnlike commercial alternatives, KeePass uses 100 percent open-source code. Nothing is guaranteed in this life, but because open source code can be examined by anyone qualified to do so, it provides the best guarantee we have that a program is doing what it is supposed to, and only what it is supposed to. In 2016 the European Commission's EU Free and Open Source Software Auditing project (EU-FOSSA) audited KeePass 1.31, concluding that "the code has a good level from a security point of view, with only a few findings, none of which were critical or high-risk in nature." KeePass 1.x differs quite considerably from KeePass 2.x, but these findings are nevertheless very encouraging. End-to-end encryptionKeePass stores passwords client-side on your desktop in encrypted. kbdx containers. They are encrypted by you, and can only be decrypted by someone with your password. Security can be farther improved by use of a key file and/or some other form of multi-factor authentication. .kbdx files are therefore fully end-to-end encrypted. They need never leave your local storage, or you can manually sync them across your devices using USB cables, memory sticks, and suchlike. This ensures that no online adversary can ever access them, even in encrypted form. For the super-paranoid out there this is great, but thanks to the strong encryption used for each .kddx file it is safe to store them in insecure online locations such as Dropbox. An adversary might able to access the encrypted .kbdx file, but good luck cracking AES-256 to open it! By default, all .kbdx files are secured using strong 256-bit AES encryption with an SHA-256 password hash function to authenticate the data. This is literally as strong as modern symmetric key encryption allows. The NIST-averse can instead use optional plug-ins to encrypt their passwords with alternative ciphers such as Twofish or Serpent if they prefer. Two-factor authentication No matter how strong the encryption, however, the weak point is always human error. Especially when it comes to passwords! With KeePass you need only remember one master password ever again, but do please make sure it is a strong one! Or even better, use a passphrase consisting of many words and spaces. Passphrases are also often be easier to remember than single passwords, which is good, because if you forget your master password then… oops. Even the strongest password (or passphrase), though, is a point of weakness. KeePass addresses this with optional out-of-the-box support for two-factor authentication (2FA) via key files. A key file is created when you create the .kbdx database, and must be present in order to open the database. A password is still required, but is useless without the key file. The key file can be stored in secure locations such on your home PC, phone, or encrypted USB stick. It should, however, never be stored in insecure locations such as Dropbox as the entire point is that only you have access to it! It is possible to further secure a database by requiring that you are logged in to a specified Windows User Account when you open a .kbdx file, but this does limit your ability to share passwords to other platforms. A number of KeePass plug-ins also support 2FA via TOTP codes sent to an authenticator app on your phone, YubiKe, smart card, and more. Ease of useWe have a detailed How to Setup KeePass tutorial. There are a few steps involved, but it's basically just a matter of following a setup Wizards which holds your hand. Once installed, you can perform all sorts of password management functions from the main console window, such as creating new passwords, arranging passwords into groups, modifying and deleting password, and suchlike.
Each password entry includes a notes section which is useful for storing any useful information securely, not just information directly relating to website passwords. It is also possible to set an expiry date for entries.
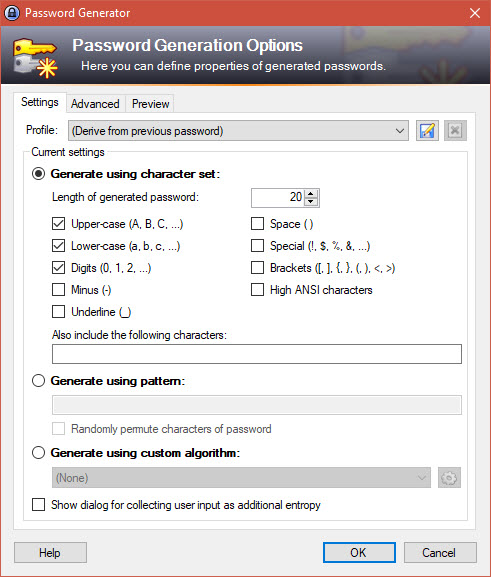
As with any good password manager, KeePass can generate strong passwords for you as needed. Some websites have very specific requirements for the passwords they accept, so it's good that KeePass allows you to tailor the kind of password that it randomly generates.
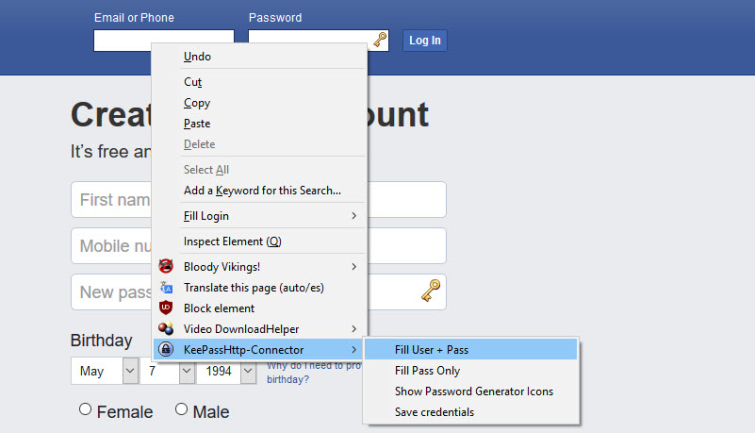
Browser integrationAn important aspect of any password manager is how easy it is to use, and since most of our online activity when using a desktop PC is performed through the browser window, this makes browser integration a central concern. KeePass does not offer any browser integration out-of-the-box, but it can be easily added using a combination of plugins + browser add-ons. A number of options are available, but we recommend KeePassHTTP-Connector for Firefox and Chrome. In our How to set up KeePass guide, we cover how to implement to KeePassHTTP-Connector browser integration. Doing this really is very simple and only takes a minute or two, but it has to be recognized that other password managers do similar things without the need for you to do anything. Once KeePassHTTP-Connector is in place, just click on a username or password field to autofill from your KeePass database. By default, new login details will be saved to the open KeePass database. A lock icon to the right of password fields (which can be disabled if you find it annoying) will generate a new secure password instantly. Final thoughtsNo other password manager beats KeePass when it comes to keeping your passwords secure. It is also completely free, and thanks to a huge range of plugins, it is by far the most extensible and flexible password manager around. We also think it is fairly easy to use. Its user interface does look rather dated, though, and it not as easy to use as many all-in-one password managers. For those with even slightly techie leanings, we recommend KeePass unreservedly. If you need a slick and idiot-proof password manager that even your grandparents can use, however, then we suggest looking at open source Bitwarden before considering commercial alternatives. |
| You are subscribed to email updates from "buy encrypted cell phone,encrypt my data,should i encrypt my iphone" - Google News. To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google, 1600 Amphitheatre Parkway, Mountain View, CA 94043, United States | |
Comments
Post a Comment