How Mesh Messaging Apps Work, and Why You Might Need One - Gizmodo
How Mesh Messaging Apps Work, and Why You Might Need One - Gizmodo |
- How Mesh Messaging Apps Work, and Why You Might Need One - Gizmodo
- Hong Kong protesters should be smarter about their messaging apps - PocketNow
- Stealthy Android Trojan Spy Signs You Up For Premium Subscriptions - BleepingComputer
| How Mesh Messaging Apps Work, and Why You Might Need One - Gizmodo Posted: 04 Sep 2019 07:10 AM PDT   A particular type of app is back in the news on the back of the Hong Kong protests: Mesh messaging apps that allow users to keep in touch without relying on wifi networks, cell networks, or any other type of infrastructure controlled by the authorities... and these apps can be useful whether or not you're trying to stay under the radar of the government. Mesh or off-the-grid messaging apps rely on device-to-device communication, rather than sending their 1s and 0s via a wifi router or cell tower. They can use Bluetooth, or ad hoc wifi (the same sort of ad hoc wifi your phone might set up when it's trying to get a smart speaker or a home security camera online). The obvious benefit is there's no one in the middle of the conversations you've got going, and that makes them much harder to monitor or control. Governments and hackers can't tap into cell towers to block channels of communication, for example, or listen in on the data being beamed to your internet service provider, or bring down websites that you're relying on to stay in touch. You'll often see these apps referred to as offline apps because they don't log into traditional online networks, or as peer-to-peer apps—they work in the same way as torrenting software does, making connections between users rather than sucking files from one central repository. Advertisement Of course Bluetooth and wifi don't go on forever, which is where these apps get really smart: They use devices that have the same app installed to pass on messages, like a relay team might pass on a baton—this is all invisible to the people doing the passing on, so it's not like your message to your mom is being read by dozens of people on the trip.  Advertisement A similar sort of principle is deployed with tracking tags like Tile, and will soon be introduced with Apple's Find My app—other users with the right app installed can be anonymously enlisted to broaden the network, whether that's to track down a missing MacBook or pass on an encrypted message. That does highlight one weakness in these apps: Wifi and cell coverage are pretty much ubiquitous, at least in urban areas, whereas you might go for hundreds of miles without finding someone running one of these mesh messaging apps. They rely on groups of users in close proximity to work effectively. Advertisement The range typically maxes out at around 100 meters or 328 feet, and that's in ideal conditions—it's less if you're inside a building or not in a direct line of sight with someone else. If cell or wifi connections do become available, these can be used to expand the reach of the network. While apps like WhatsApp, iMessage, Signal, and others use end-to-end encryption to stop spying, these offline messaging apps go one step further to avoid relying on the traditional networks completely. They're harder to shut down as well as being difficult to monitor. Advertisement And as we've said, you don't have to be trying to stay one step ahead of the authorities to make use of these apps. They can also come in really handy when you're out on a camping trip without access to cellular networks, when there's a power outage or some kind of natural disaster, or when you're on a cruise ship or airplane. You could even use them with friends and family at gigs and festivals.  Advertisement Of the many peer-to-peer messaging apps available, Bridgefy for Android and iOS seems to be the most reliable and the one that's most actively developed right now (it also licenses its technology out to other app makers). Besides offering one-to-one communication, it also lets you broadcast messages to everyone in a certain area—a bit like a status update that anyone around you is able to pick up. Another option worth looking at is Briar, which is only on Android. It's simple but it's slick, and it's designed specifically for activists, journalists, and "anyone else who needs a safe, easy and robust way to communicate"—to that end it uses the Tor network, if an internet connection is available, to prevent outside monitoring and eavesdropping. Advertisement In the past, Firechat (Android, iOS) has been mentioned as one of the leading mesh networking apps, and it features options for discovering people and groups near you besides accessing the contacts you already know. However, recent updates seem to be buggy and we weren't able to get it to work. There's a hardware angle to this as well: Using a device like the goTenna Mesh (yours for $179) you can create your own off-the-grid, peer-to-peer network and have your phone connect to that rather than wifi or a cell network. That means any app on your device could hook up to the mesh—provided of course that the people you wanted to speak to also had goTenna Mesh devices with them. Advertisement It's obviously not going to replace your day-to-day communications, but a device like this can be useful if you're out camping, or if the traditional networks are down for whatever reason, or if there are a handful of people you need to keep in touch with locally—and the range is four miles (6.4 kilometers). |
| Hong Kong protesters should be smarter about their messaging apps - PocketNow Posted: 04 Sep 2019 07:00 AM PDT Apparently there are some major pro-democracy protests going on in Hong Kong right now. The protesters need to be able to communicate with each other, but the government is constantly spying on them (and all residents) by monitoring internet traffic, email traffic, SMS text messages and phone calls. They could probably encrypt email if everyone had public keys and private servers, but that's way too complicated and problematic. Plus the metadata would still be visible. When the protesters are all near each other, they have hand signals that get passed along the chain for emergencies like getting a helmet for someone or clearing a path for ambulances, but hand signals aren't sufficient for everything. As seen in this Forbes article, many of the Hong Kong protesters have started using an app called Bridgefy which doesn't require a persistent internet connection and instead transfers messages via short-range Bluetooth. To transfer messages across distances longer than 30 feet (or maybe 330ft), the messages hop from phone to phone via Bluetooth in a "mesh" network. In other words, each user's phone acts as a node or connection point for transferring information. It's kind of like the "telephone" game some kids play where you line everyone up, one person on the end makes up a message, whispers it to the person next in line, and everyone repeats until the message gets to the end of the line. No internet connection or centralized server required! (It's just like how the real internet works except each phone is a server/relay.) That sounds pretty smart, but here's the problem… Bridgefy requires a connection to a central server when registering your app… and WORSE, it uses your phone number for registration… AND sends an SMS text message to confirm that registration. All three of those things are very bad ideas if you can't trust your phone carrier to keep your information private. First of all, the state could easily block internet access to the centralized server that makes Bridgefy app registration possible. It will still work for the people who have already registered of course, but new registrations could easily be disabled. Next, it's always a bad idea to put your real phone number into any kind of external database. Who knows what they'll do with it? And your phone number can easily be used to identify you and track many things that you do with that phone number. (You could also get SIM swapped and lose lots of money and access to many of your other digital accounts, but that's another story.) Furthermore, you have no way of monitoring who does what with your phone number! As an aside, if you use email as a personal identifier online, you do have much more control over knowing who does what with that address because you can freely create email aliases for every external database that you register with. Many people do this, not only to understand who sells their contact info to other people/companies, but to also be able to block them by deleting the compromised alias. For example, if I make a specific email alias address for only Facebook use, then I start getting emails from somewhere other than Facebook, now I know that Facebook is the one that shared my contact info. You can't really do that with phone numbers. Now back to the original topic… Thirdly, if the government is monitoring SMS messages, then they can easily make a list of all of the mobile carrier account cell phone numbers that are using the Bridgefy app based on who the registration confirmation SMS was sent to. (There is a secret way to skip the SMS verification by repeatedly entering a wrong number until a "skip verification" button appears, but signup still requires registration with a centralized server on the internet.) Then if any of these protesters are using Bridgefy on a mobile phone account that was paid for using their real name or using a credit card registered in their real name, then the government can find out everything about them… call history, family members, purchasing habits, income sources, etc. At that point, you're probably not nearly as secure as you would want to be when you're fighting for freedom. Why not Briar?There's another messaging app called Briar that sounds like it was specifically designed for technological and internet freedom fighting. This app does a similar "mesh network" thing where messages are transferred via Bluetooth without requiring full internet access, but it also supports transferring messages over peer-to-peer WiFi networks as well as the internet-connected onion router network (Tor). With Briar, all messaging is peer-to-peer only with full encryption. None of your information goes to a centralized server. Furthermore, you don't have to put any personal information into Briar. All you need is a made-up name and password, and the password isn't sent anywhere. It's only there to secure the app on your device. Well, okay… there is one catch. Since it can't (shouldn't) use your phone's contact list of phone numbers to match you with friends to talk to, it uses a much more secure method of establishing connections between people.  Emailing screenshots of the "add contact" QR codes doesn't even work. At least for the first contact, both people have to actually physically be face to face in order to make a connection in Briar. You enable a connection by scanning the other person's QR code that they can display within their Briar app. Then they scan your QR code and the connection is available for as long as you have the app installed. Once you have some real-life contacts added to the app, you and your contacts can "introduce" other contacts within the app without having to physically be standing next to them. This method of contact requests makes it much more difficult for adversaries to infiltrate since you would physically have to know someone in order to be allowed into the network. It also makes it difficult for bad-actors to impersonate others.
Being able to send encrypted messages via an ad-hoc mesh network of WiFi and Bluetooth phone radios is pretty great, but what if someone is further away and out of range? Briar also allows messaging via The Onion Router network. I imagine someone in the mesh network needs to be connected to the internet in order for this to work. The Onion Router network, or Tor, sends internet traffic over numerous relays that each obscure and encrypt different parts of the traffic in order to anonymize the source of the traffic. Tor does not hide the ability for others to see that Tor is being used, so a government could certainly block the Tor circuits within the country's internet. To get around that, there are also some "bridges" that can be used within Briar. Of course, you can turn off Briar's ability to use the public internet completely and rely solely on the local mesh network if you want. Briar even integrates with the Ripple Panic Button software which allows you to create one button that does a series of modifications to whichever apps you choose. With Briar, you can set the panic button to either simply lock and sign out of the app's connection, or you can also make it completely wipe your Briar account, messages, and contacts from the device. If you delete the account, you (and no one else) will be able to access the messages or contacts, and you'll have to go meet your friends in real life again in order to add them back. Both Briar and Ripple are available in the Google Play Store, but it would probably be smarter to install them from an APK download via their websites, or via the F-Droid repository since those are less likely to associate the installations with your personally identifiable Google account. Also, perhaps the caveat that may be preventing the Hong Kong protesters from really taking advantage of Briar may be that it is not available on Apple's iOS. It only works on Android-based operating systems at the moment. Although, if you're interested in technology freedom, you probably shouldn't be using Apple products. Lead photo source: Lezsander Discuss This Post |
| Stealthy Android Trojan Spy Signs You Up For Premium Subscriptions - BleepingComputer Posted: 04 Sep 2019 02:41 PM PDT
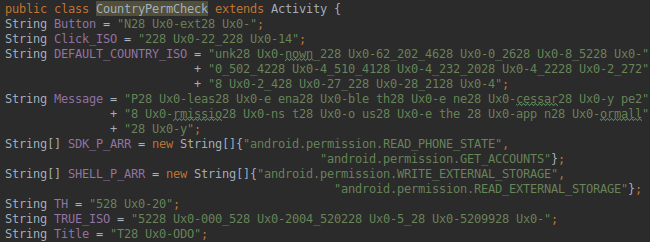
Security researchers discovered a new Android Trojan with malware dropper and spyware capabilities in 24 Google Play Store apps with more than 472,000 downloads in total. The new Android malware dubbed 'Joker' is hidden within advertisement frameworks used by the compromised apps — some with over 100,000 installs — and it is designed to download a second-stage component as a DEX file that adds more capabilities. This additional malicious component which simulates user interaction on ad sites, and will also harvest its victims' device info, contact list, and text messages. "The automated interaction with the advertisement websites includes simulation of clicks and entering of the authorization codes for premium service subscriptions," as CSIS Security Group recently found. Joker utilizes its SMS collection module to sign its victims up for premium subscriptions using the authorization codes automatically extracted from the authorization text messages. 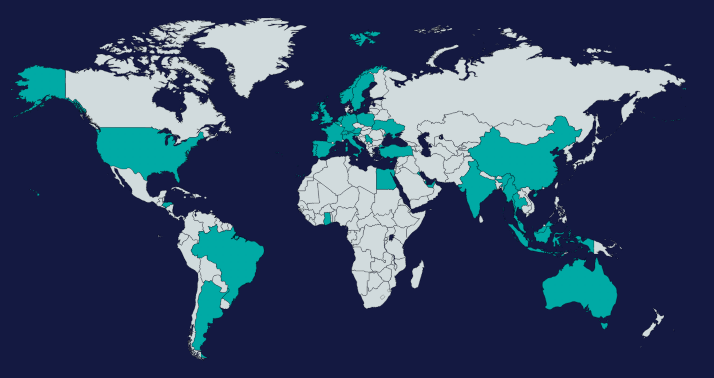 Only Android users from a very specific list of countries are currently targeted by the Joker Trojan — including but not limited to Australia, France, Germany, India, the UK, and the U.S. — with the vast majority of infected apps found by the researchers containing a hardcoded list of Mobile Country Codes. The malware compares the SIM card's country code with the hardcoded list to check if the victim is from the targeted countries and the second stage component to be dropped. However, "most of the discovered apps have an additional check, which will make sure that the payload won't execute when running within the US or Canada." The campaign's operators also send commands and code to be executed via JavaScript-to-Java callbacks on compromised devices, a technique used to protect the Trojan against static analysis. An additional method making analysis harder is the use of "custom string obfuscation schemes for all of the configuration, payload, communication parsing procedures."
Joker's second stage component periodically checks for new commands to execute by reaching out to its command and control (C2) server based on a pre-defined schedule and will proceed to open the domains with premium offers sent by the campaign's operators. The authorization codes to sign its victims up for various paid subscriptions are harvested by interacting with the premium offers pages or by texting premium numbers using offer codes found on the advertisement pages — they will also be exfiltrated to the C2 servers for a yet unknown reason. This malicious component is also the one responsible for collecting all the victim's contacts from the phone's address book, contacts that will get sent in encrypted form to the attackers' data storage servers. 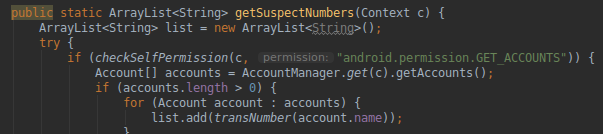 While Joker started being active around early June based on DNS metadata information related to its activity, " the major version digits in the build names give an impression of a slightly longer life cycle, potentially with more campaigns in the past." Google has removed all Joker-infected apps from the Play Store while CSIS Security Group was analyzing the Trojan's activity without the researchers having to report any of them. This shows that the Google Play Protect built-in malware protection and Google's security researchers can discover and actively remove previously undetected malware strains from the Play Store although some sneak in undetected once in a while. For instance, during last month, researchers spotted a Trojan Dropper malicious module hidden within the Android app CamScanner which was downloaded over 100 million times by Google Play Store users. Previously, a clicker Trojan bundled within over 33 apps with another 100 million downloads were also distributed via Google's official Android store, as was an Android app with spyware capabilities borrowed from the open-source AhMyth Android RAT twice over a period of two weeks. A full list of indicators of compromise (IOCs) including malware sample hashes, C2 domains used by the attackers, and the package names of infected Android apps are available at the end of CSIS Security Group's analysis of the new Android Joker Trojan. |
| You are subscribed to email updates from "cryptography app,encrypt contacts android,how do you encrypt a phone" - Google News. To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google, 1600 Amphitheatre Parkway, Mountain View, CA 94043, United States | |


Comments
Post a Comment